Affiliate links on Android Authority may earn us a commission. Learn more.
iPhone vs Android: 10 things iOS does better

The iPhone vs Android debate continues in 2025. Here at Android Authority, we can name many reasons why Android beats Apple’s mobile operating system any day. Google’s alternative offers a more open platform, choice, value, versatility, innovation, and customization, to name a few things. But what keeps iOS users hooked to iPhones if Android is so much better?
While many argue it’s a branding and status thing, we believe reasons go beyond vanity. We are tech lovers before anything else and have to accept there are certain things iOS does better than Android. Let’s talk about them.
iOS is generally faster and smoother

Having used both platforms daily for years, I have encountered fewer hiccups and slow-downs using iPhone vs Android devices. Performance is one of the things iOS usually does better when comparing iPhone vs Android. This seems ridiculous, considering iPhone internals. The iPhone 16 Pro Max is currently the most powerful Apple smartphone, featuring the Apple A18 Pro SoC. It also only has 8GB of RAM. This may not sound impressive, but we tend to get a little lost in the specs and often forget to look at what matters. Performance doesn’t only come from powerful specs. There is more to processing power than cores and speed clocks.
Having used both platforms daily for years, I can say I have encountered way fewer hiccups and slow-downs using iOS.
We ran our benchmarks on the iPhone 16 Pro Max, comparing it to its main competitors, and found that it does better than the Google Pixel 9 Pro XL and Samsung Galaxy S24 Ultra in most areas.
Whether Apple processors are better or not, what matters most is iOS is optimized to work perfectly with the few devices Apple makes. Meanwhile, Android is baked into a sea of smartphones, tablets, and other products. It’s up to OEMs to optimize the software for the hardware, and they sometimes do a poor job at it.
Apple’s closed ecosystem allows tighter integration, so iPhones don’t need super powerful specs to match the high-end Android phones. It’s all about the optimization of hardware and software. Since Apple controls production from beginning to end, it can ensure resources are used more efficiently. Furthermore, developers have to follow a stricter process to release apps, not to mention they don’t have to optimize their apps for what may seem like an infinity of devices.
This is not to say all iOS devices can outperform all Android devices. Some Android phones are made with beastly internals and stunning performance. Generally, though, iOS devices are faster and smoother than most Android phones at comparable price ranges. Even the budget iPhone SE is a great performer, costing only $429.
iOS is super simple to use

Sometimes, what we love about Android makes it a less enticing platform to the general consumer. Google and its partnered manufacturers have improved at making Android more intuitive. But even after Android 12’s major design overhaul, it can still be confusing. Dealing with random icon placements, endless settings, and full customization isn’t for everyone. Furthermore, inconsistency between phone makers creates a learning curve, as most Android phones look and feel different from one another.
Apple fans love the simplicity of their operating system, and it is arguably one of the things iOS does better in the iPhone vs Android battle. There isn’t much to iOS, and that’s part of the allure. Many iPhone lovers don’t want a phone to mess around with and customize. They want a device that works well, is easy to use, and can take them to their content with the least amount of effort. This is what the “it just works” saying is all about.
That said, customization lovers are also getting some love from Apple with iOS 18. This software upgrade introduced the ability to change icon colors, as well as place icons wherever the user wishes.
Some things never change, though. There’s still no app drawer to hide things — it’s all laid out before you. The settings are straightforward, and the experience is always pretty much the same, no matter which Apple mobile device you use.
The user experience for iOS is intuitive enough to have almost no learning curve. I have seen kids who have never used a smartphone figure out the basics in 10 minutes. Some of these kids learn how to use an iPhone before they learn to read! Similarly, if you already own an iOS device, you can switch to any other and immediately know exactly how it works.
Timely updates

Updating software is one of the things iOS does better than Android. If your iOS device qualifies to get the latest update, it will get it as soon as it launches. This can be bad news for older devices that can’t handle more resource-intensive iOS versions very well. That is another topic and something to worry about only if you have a significantly older Apple device, though.
The updating process isn’t as seamless with Google’s Android ecosystem. Google only gives direct updates to its own products, like the Pixel smartphones, and even those have been known to fail at getting updates efficiently sometimes.
Manufacturers like Samsung, Sony, Motorola, and all others have to get the update from Google, work on it, optimize it for your device, and then send it out. In many instances, carriers have to go through them too, which only assures you get updates later, sometimes months down the line… if ever.
Additionally, iPhones have historically been supported for much longer. Apple usually keeps updating its devices for about six or seven years. For example, the oldest devices to get iOS 18 are the iPhone XR and XS, which were released in 2018. It wasn’t until recently that manufacturers started competing with Apple in this department. The best update promises in the market come from Google and Samsung, with seven years of updates. This is not a common practice in the Android market yet, though, and lower-end devices still tend to have lackluster update promises.
The Apple ecosystem

This one is more of a tie in the iPhone vs Android debate, because Google has improved integrating its services across devices in the past few years. Regardless, Apple products like iPhones, iPads, Apple TVs, Apple Watches, and Mac computers are tightly integrated with iCloud, iMessage, FaceTime, and other in-house services. While Google has its competing services, which work great, too, they have a learning curve and don’t feel as intuitively connected.
Some apps required to access core Google services aren’t pre-installed, forcing users to hunt for them in the Google Play Store. This may not seem like a massive deal to most tech-savvy users, but it can be a daunting task to some, or at the very least, an annoyance.
Speaking of app stores, the Apple App Store is significantly better curated and better policed than the Google Play Store. Developers looking to get their apps on the App Store have to go through a long and expensive list of checks and procedures, but the result is a net increase in the overall quality of iOS apps. The Apple App Store is generally cleaner, has fewer ads, and offers cool extra features like interviews, guides, better app lists, etc. It may be a walled garden, but it’s a safe, familiar, and easy-to-navigate garden all the same.
You get much more accessory options with iPhones
Apple devices usually have a much wider variety of accessory options, giving Apple another win in the iPhone vs Android debate. It’s just much easier to create cases and other accessories for the few iPhones available. Any manufacturer will have a very hard time trying to release a specific case model for all the Android devices available. IPhones tend to dominate the market, so accessory makers usually focus on these Apple models first, as they are in the most demand. This applies to cases, screen protectors, MagSafe batteries, wireless chargers, and other accessories.
Of course, the accessory market is very healthy on the Android side, but it just isn’t as expansive. Additionally, things get much more complicated if you move away from the popular devices. For example, you will have a good selection of cases available for the Google Pixel 9 Pro XL. You can’t argue the same about less popular Android phones, which there are plenty of. On the other hand, no matter which iPhone you have, there is a sea of accessory options you can choose from. And accessory makers will almost always release products for iPhones first.
Apple also has MagSafe, which allows you to attach accessories to the back of the device magnetically, and can even be used for wireless charging. Yes, you can use MagSafe accessories with Android, but the magnets won’t work well unless you get a specialized case or adapter. Thankfully, similar functionality will be introduced to Android soon, thanks to Qi2.
Apple CarPlay
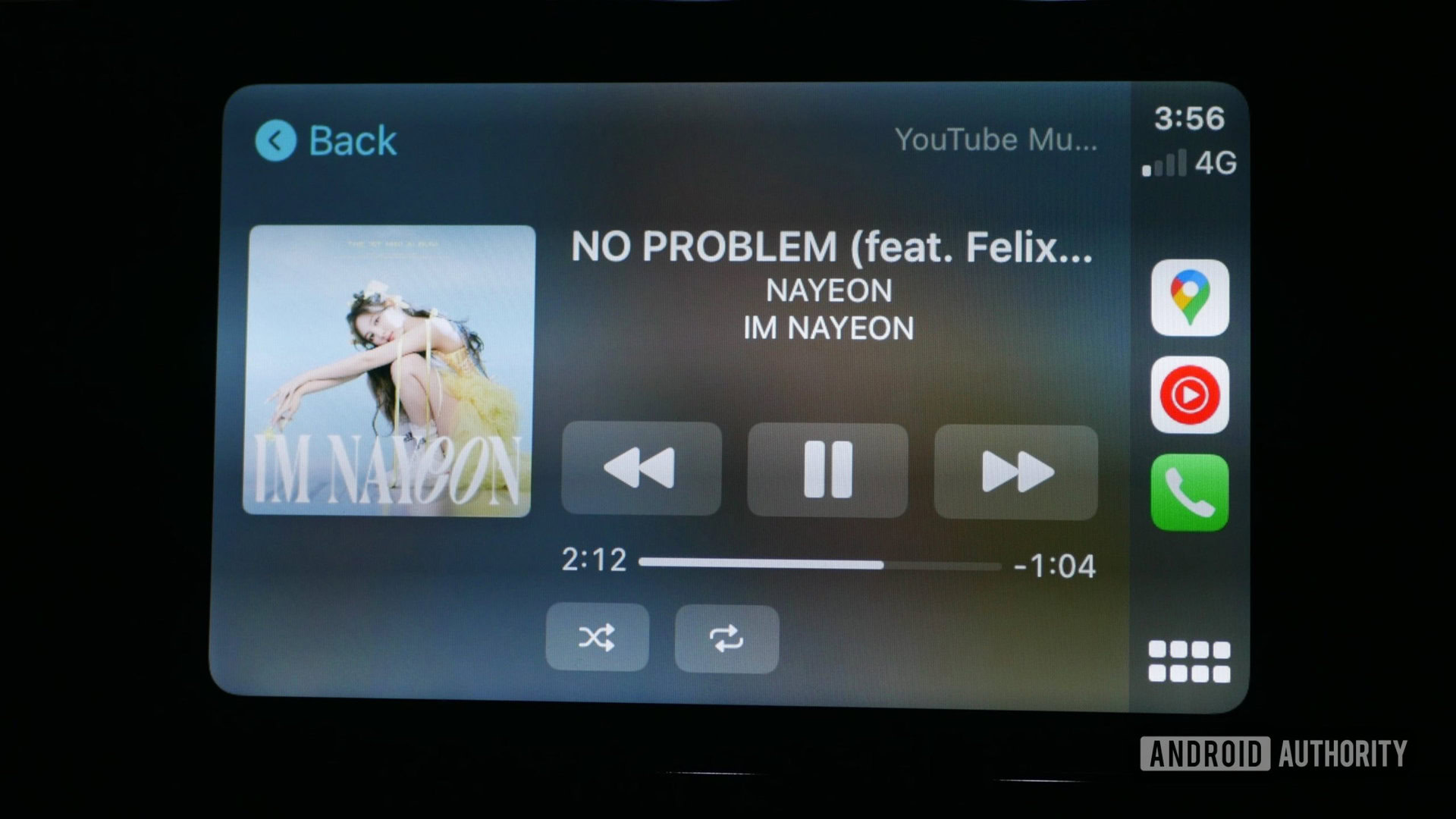
If you care for in-vehicle functionality, this is an important factor in the iPhone vs Android debate. No matter how often I give Android Auto a chance, I keep returning to Apple CarPlay. Sometimes, I carry an iPhone just to use CarPlay!
Apple’s alternative has neatly arranged icons. You can move these icons around to prioritize your favorite apps for easy access. Sounds familiar? Yep, it works much like iOS on a phone or tablet! Some things have been moved around, but the experience is much more uniform.
Android Auto has moved away from its totally random interface based on recommendations. It’s now more similar to Apple Carplay, as it has a list of apps you can easily access. It’s still a bit more convoluted, though. Not to mention, Android Auto’s performance seems to lag despite sometimes using some of the most powerful phones in the market.
Google Assistant does a much better job than Siri, but that feature does not draw me away from Apple’s in-vehicle solution. Apple CarPlay is better looking, more straightforward to use, and more functional.
Also, I am always running into odd bugs with Android Auto. Sometimes, Google Assistant just won’t work, music won’t play, or there are audio issues. I also get random disconnects in the middle of my drives very often. I’ve tried it all! I can’t, for the life of me, ever figure out what’s going on. I just resort to disconnecting and reconnecting the device. Sometimes I have to restart the device or the car, altogether.
Superior support

Apple leads the way in tech customer support. AppleCare may be expensive, but insurance claims for iOS devices are an absolute breeze. If you have a local Apple Store nearby, you can often walk out with a brand-new device in less than an hour.
Speaking of Apple Stores, love or hate them, Apple’s retail locations have a signature look that many retailers have tried to copy. The open-plan design draws you in as soon as you walk by. Many staff members are on hand to help you with any purchase or problem. They even have free classes to teach you how to use Apple devices.
No company is perfect, but having an iOS phone or tablet sure beats the competition if you ever have a problem. You don’t need to go through carriers, look for weird customer service phone numbers, fill out online forms, send faxes, stay on hold for long periods only to talk to a robot, or wait weeks for a fix or replacement. Go to your nearest Apple Store and enjoy their well-known customer service. Easy as (Apple) pie.
Resale value

Affordability is not precisely one of the things iOS does better than Android, but Apple has a market advantage over most of its mobile competitors. iPhones, iPads, and other Apple products typically hold their value much better than Android products. Even if it is more expensive, buying an iPhone is often a better financial decision in the long run. You can sell your used Apple device for more when it’s time to switch devices. And because Apple products are so popular, they usually sell much faster.
iPhones, iPads, and other Apple products typically hold their value better than Android products.
Let’s put things into perspective with some real-world examples. The iPhone 12 Pro Max launched in November 2020 for $1,099. It’s selling for about $230 to $380 in good condition now. That would be about 21% to 35% of its original value. The Samsung Galaxy Note 20 launched in August 2020 for $999. It sells for around $105 to $230 on eBay. This equates to about 11% to 23% of the original value. Big difference, right?
Keep in mind that this example is a best-case scenario for Android. Samsung is another brand that keeps its value better than others in its class. The resale value favors Apple far more than other smaller Android manufacturers.
Apple AirTags

Another important factor to consider when deciding between iPhone vs Android is Bluetooth trackers. These little gadgets can track and locate items. We’ve seen competitors release very similar Bluetooth trackers, and you can even argue they can be better in some ways, but Apple has something no competitor can match. Apple’s network of devices has much more coverage wherever you go.
The real problem is that all these trackers are limited in terms of the devices that can track them. Some of the best Apple AirTag alternatives, like the Samsung Galaxy SmartTag2 and Tile trackers, work within their ecosystems and through their apps. Apple AirTags can also be tracked only by Apple devices. Still, the difference here is that Apple devices are so prominent that any tracker is likely to be close to an iPhone anywhere it is. Apple has opened its Find My network to third parties, meaning other tag or accessory manufacturers can make Find My trackers.
Apple AirTags also integrate amazingly with iOS. It’s pretty much a system function and requires no extra apps or downloads. Setting it up is quick and easy, and works by simply tapping your iPhone on it. And the best part is that, while AirTags cost a bit more than the competition, the difference isn’t significant, and it ends up being a much better product anyway.
Google has also opened its Find My Device network, which looks promising for the future, as there are also many Android devices out there. That said, options are still growing, and the ecosystem isn’t as mature as Apple’s quite yet.
Contactless payments
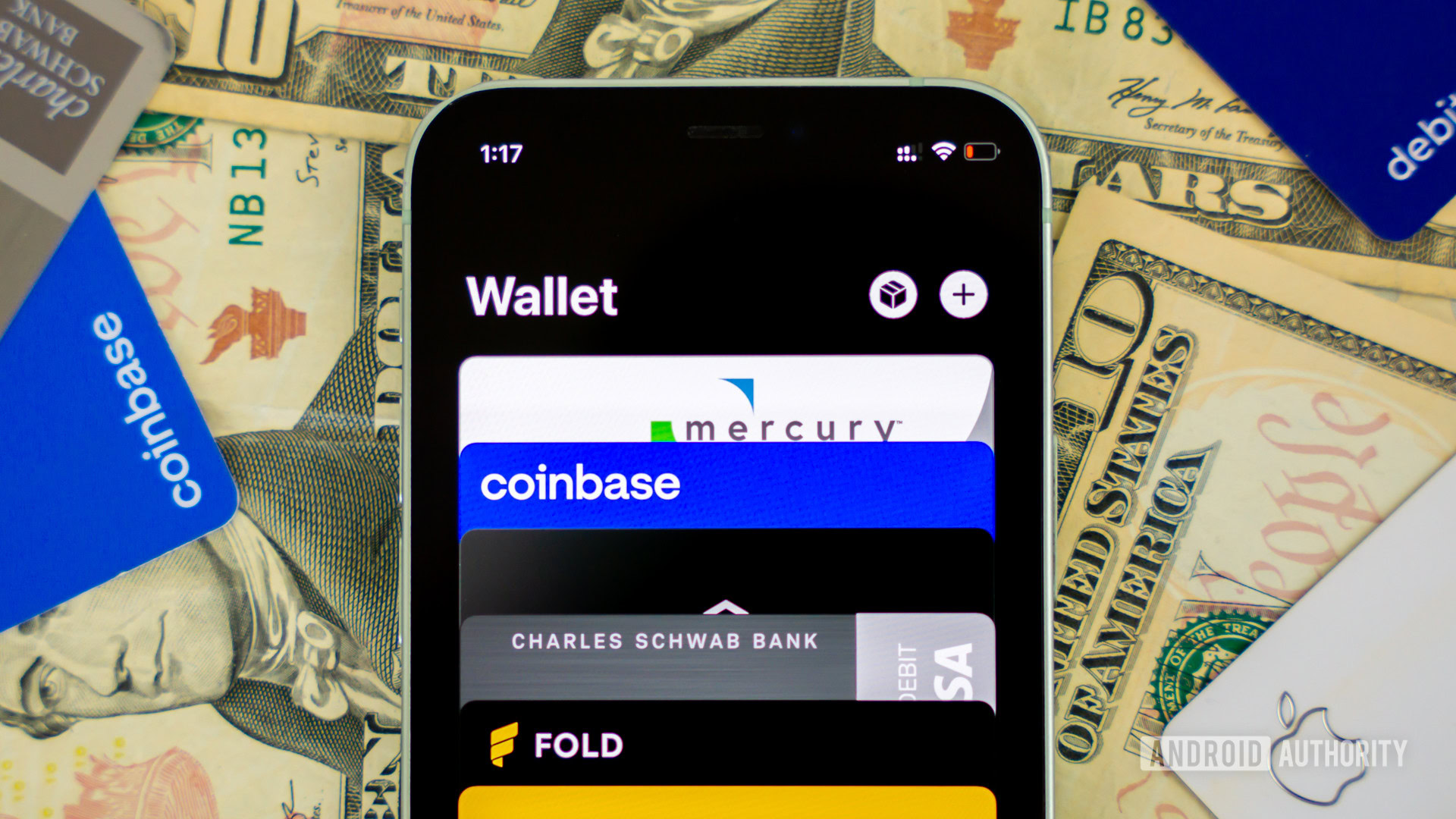
Google Pay works well, but the app is much more convoluted. In older software versions, it sometimes wasn’t even pre-installed on Android phones! The service has taken a backseat and is no longer getting much attention, even from Google.
Regardless, all contactless payment services work well, but Apple Pay seems to be the most polished option out there. It works seamlessly across Apple-made smartphones, tablets, and even smartwatches. Apple Pay is also more supported by banks and credit card companies out there, especially the smaller ones, which are the ones that usually skip Google Pay and other solutions. It’s also accepted by over 85% of retailers in the USA.
Furthermore, Apple now offers its credit card, which provides some pretty good benefits. For starters, you get 2% cashback on Apple Pay purchases and up to 3% back with some retailers (including Apple). However, the Apple Card can only really be fully managed through iOS, using Apple Wallet. Some people will think twice before letting go of the Apple Card and moving to an Android device.
iPhone vs Android FAQs
Well, of course! We love Android around here, and have many great things to say about Google’s mobile OS.
- More device availability: From affordable handsets to rugged and gaming options, Android has it all.
- Usually better battery life: While they have pretty good battery life, iPhones focus on design, not so much on battery life. Plus, there are Android phones with huge batteries.
- Customization: You get a bevy of customization options with Android, as well as access to launchers and even custom ROMs.
- Innovation: Breakthrough features tend to come to Android before they reach iOS.
- Form factors: The Android market is more adventurous in terms of design. There are still no foldable phones from Apple, for example.
- More control: iPhone settings can be a bit limiting. Android has expansive settings with a plethora of options.
- More third-party apps: While Apple has a better app store, some apps can’t make it into the walled garden. With Android, you can use other app stores and even manually sideload apps.
- Better file management: File management has always been better on Android, and you can opt to use other third-party file managers if you prefer.
- Physical SIMs: The newer iPhones don’t come with physical SIM card slots in the USA. These include the iPhone 14, iPhone 15, and iPhone 16 series. Some of us still prefer physical SIM over eSIM.
- Google Assistant: While Siri is nice, many of us believe Google Assistant to be superior. Especially now that Gemini is coming into the game.
According to Statista, as of the first quarter of 2025, Android holds about 71.88% of the mobile OS market share. iOS makes up for 27.65%. These numbers refer to the worldwide market share.
If you want to know about US-specific statistics, Android holds about 60%, while iOS makes up 40% of the market share.
Thank you for being part of our community. Read our Comment Policy before posting.
