Affiliate links on Android Authority may earn us a commission. Learn more.
How to protect your privacy using Android

We keep an awful lot of personal information on our mobiles these days and, as a direct result, these devices know quite a lot about us. From our location and contacts to our favourite hangouts and hobbies, we happily exchange some of this information for “free” services from the likes of Google and others, but there are plenty of less scrupulous people and businesses out there that would also like to get their hands on this valuable asset.
Read Next: How to update your Facebook privacy settings
These days, it makes a lot of sense to look after the data stored on your smartphone and fortunately there are plenty of handy tools available within the Android ecosystem to help keep your data private.
Use the lockscreen
Using a basic PIN, password or swipe gesture really is the bare minimum level of security that everyone should put on their smartphone. As shocking as it might sound, data from a reputable survey in early 2016 suggested that 34 percent of all Android users don’t even make use of the basic lockscreen feature that is built into every Android smartphone. Granted, this may have increased since then, but it still illustrates an important point — not everyone takes security as seriously as they should.

While the talk about malicious software, bugs, and backdoors may often make tech headlines, physical phone theft is still a real issue. If a criminal lacks a conscience enough to steal your phone, they probably won’t have too many qualms about sifting through your contacts, pictures, and emails in an attempt to grab personal data that would be used for further exploitation. There’s a good chance that you’re making use of a banking app on your phone too, and you really wouldn’t want someone to get into those types of important and personal apps.
Read Next: 10 best privacy apps for Android
Enabling a lockscreen PIN is incredibly simple, just head on over to Settings -> Security -> Screen Lock. Here you can pick from your preferred password lock type, which you will then need to enter each time you try to access your phone. Other manufacturers may move this menu to under general settings, if they have their own lockscreen protection alternatives, such as LG’s knock code. And of course, a lot of phones these days give you the ability to log in with other methods like your fingerprint, if passwords aren’t your think.
Device Encryption
Applying a password to your phone’s lockscreen is a start, but particularly nefarious and skilled criminals may still be able to access your files, given enough time and access to say a stolen smartphone. Device encryption can be used put all of your files into a format that cannot be understood without first decrypting them with the proper key, or a password that only you will know.
Read Next: 10 best security apps for Android that aren’t antivirus apps
Encryption is a really tough form of security, hence why the FBI doing battle with Silicon Valley companies in an attempt to bypass it. However, it comes with a bit of a performance penalty on some older smartphones, although newer devices shouldn’t notice any issues.
Much like the lockscreen, encryption options can be found under the Settings -> Security menu, where you will find options to protect both the data on your smartphone and microSD card, if your device has a slot. Encryption can take a little while, so best to start up the process with a full battery and plenty of time to spare. For more information and a walk through of the steps, check out our encryption guide below.

Find my device
While we are dealing with taking precautions against stolen smartphones, all Android users should take a little bit of time to check out Google’s Find My Phone feature. Previously known as Android Device manager, this service is linked up with your Google account and can be used to manage all of your Android devices remotely, providing that they are connected to the web.
Find My Device can be logged into through any web browser via this link. From here you will be presented with a list of your devices, with options to track their location, make them ring in case your phone has stuffed itself down your couch, or to “enable lock and erase”. By enabling this last feature you will be able to remotely lock your smartphone or tablet, and even completely erase all of the data on the device if it’s stolen.
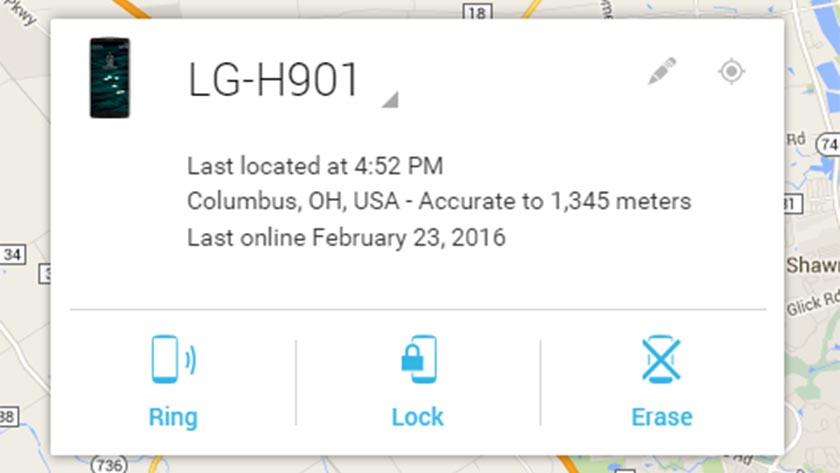
You can also find these same settings directly on your device. Head on into “Google Settings” and tap Security. Under Find My Device you can review and edit options for remote locking and erasing.
Picking tougher passwords
Along with just plain out not using a lockscreen, weak or commonly used passwords are the biggest no-no if you’re looking to keep your data secure, both on device and online. Lists of the most commonly used passwords are published rather frequently and if your password of choice appears on that list, you should really change it. Disappointingly, the most common passwords rarely change, so here are some to definitely steer clear of:
- 1234567 (and other basic counting variations)
- password
- qwerty
- football
- welcome
As a general rule, a mix of cases, numbers, and special characters (where allowed) makes for the most secure password, and the longer the better too. 8 characters is really the bare minimum recommended, but moving up to 12 or 16 makes them so much harder to guess.
Read Next: 10 best applocks and privacy lock apps for Android
A strong password is a good start, but using multiple passwords is even better. You’ve no-doubt heard about sites being hacked and passwords exposed, so it’s not very safe these days to rely on the same code for all of your accounts, apps, and websites. Of course, keeping track of all these different passwords can be a nightmare, but there are a number of apps out there that can help manage them all and can even generate very strong random passwords.
Android apps like LastPass, mSecure, oneSafe, and Keepass2Android each offer up their own selection of unique features for additional security. These include secure password storage options, two factor authentication, and multi-device support, among others.
VPN (Virtual Private Networks)
So far, we have mostly dealt with offline security and preventing thieves from cracking into your private files. However, it’s also possible for the bad guys out there to track exactly what you’re looking at and downloading online.
Read Next: 15 best Android VPN apps
One way around this is to use a Virtual Private Network (VPN). Instead of communicating directly with every website that you visit, a VPN service will route your traffic through a different server or selection of servers first. This way, your IP address and device are not immediately connected to an end service, although it doesn’t stop somebody from tracking the chain further back if they are really that interested in what you were up to. Some VPNs will also keep a log of what you’re up to, so always best to check out the terms and conditions before you use any service.
VPN’s add an extra layer of privacy, but they don’t make you completely invisible. They are also commonly used to access websites that are locked to a specific region, such as on demand video streaming services. However, you will often find that your internet speeds slow down quite a bit because of all the diverted traffic.
There are a number of free options out there, but most of these come with a catch. You know the saying, if the service is free then assume that you’re the product. Instead, picking a paid for option will likely result in faster browsing speeds and better privacy. We recommend ExpressVPN, it’s secure, fast and reliable with apps for all your systems including Android/Windows/Mac/iPhone. See our Express VPN Review.
Another very high quality VPN service is IP Vanish, which we’ve lately found works particularly well on Android. Although a little pricier, IP Vanish keeps no logs and has minimal browser slowdown.
Encrypted Communications
While VPNs can offer some degree of privacy, the only sure fire way to know that no unwanted eyes are snooping in on your communications is to use encryption. Several Android apps have incorporated encryption into their messaging services to varying degrees, with uses ranging from simple text messages to video calls.
Read Next: How can you use Android, but not be tracked by Google | 5 best private messenger apps for Android
Much like device encryption, these apps can scramble up communications into a form that is virtually impossible to decipher without the correct key. This allows for messages and files to be sent between parties over the web and only unscrambled at each end with the correct matching key. This method is very effective at keeping information secure, so much so in fact that law enforcement agencies around the world are rather hostile to it.
A number of commonly used mobile messaging services use some form of encryption, including BlackBerry Messenger, Facebook Messenger, Skype, Snapchat, and WhatsApp. For non-web based communications, you can try the open-source Signal Private Messenger for calls, SMS and MMS.
However, many of these apps aren’t using end-to-end encryption, whereby the keys are only known to the devices at each end. Instead, a lot of the most popular services use server based encryption. So while outside lookers won’t be able to unscramble any intercepted communications, the service provider likely knows the key to decrypt your messages and will therefore be able to understand and share your communications with third parties, such as law enforcement agencies, if so requested.
You can take a closer look at exactly how secure a number of these encrypted data apps actually are over at the Electronic Frontier Foundation’s handy Secure Messaging Scorecard.
Understanding App Permissions
Now that we’ve dealt with general data privacy, the other major snoopers in the mobile space are actually the apps that we all download. Of course, you should always install software only from trusted sources, such as the Play Store, but even then some apps, especially the free ones, exist to turn your data into profits. Ad supported apps are one thing, but digging through your files is another.
Read Next: How to tweak your Instagram privacy settings
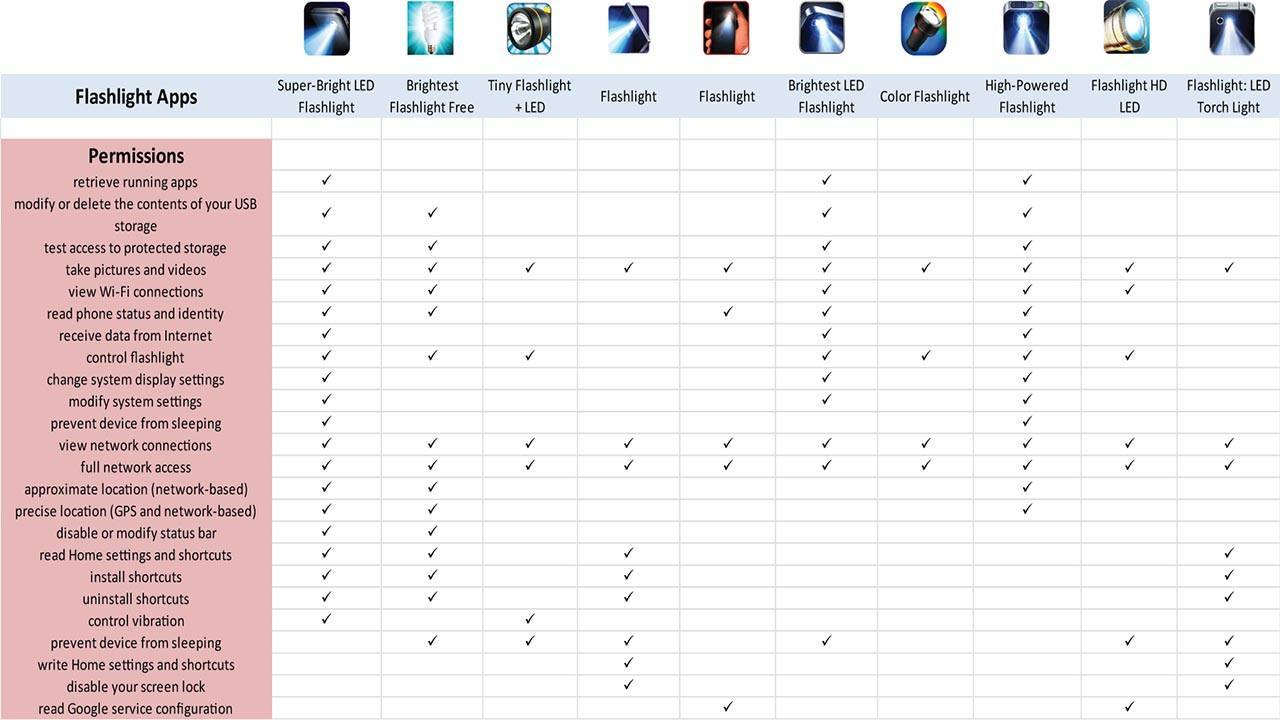
One big hint that an app may be up to something dodgy is to check out the permissions that the app requires upon installation, and think about what makes sense for the features that the app is offering you. A classic example is the range of popular flash-light apps available, with many requesting access to USB storage, WiFi networks, data, and Google services, none of which really have anything to do with turning a flash-light on or off.
Unfortunately this is a rather grey area, with some permissions being required to perform certain tasks that might not immediately seem key to the app’s main purpose. Top notch app developers should explain why certain permissions are needed in the app’s description, but this is not as common an occurrence as it should be.

With the introduction of Android Marshmallow users can actively manage which features apps have permissions for. To do this, simply head on over to Settings -> Apps -> click the gear icon -> App Permissions. However, not all apps have been updated to comply with the latest Marshmallow API, so disabling some permissions may break older apps. Expect to spend some time on trial and error here.
Anti-virus apps
While the Play Store does a very good job at screening out malicious applications, additional security can be had with the range of anti-virus apps available from the store. This isn’t really necessary for most users, but if you’re big on side-loading apps from other developer websites, then anti-virus is certainly worth looking into.
Read Next: 15 best antivirus apps for Android
Of course, the free versions are probably going to be collecting some data to sell for advertising purposes, so those versions defeat the purpose of our article. But there are a number of reasonably priced options available that also introduce some additional features.
Many anti-virus apps pack in anti-theft features these days, including remote phone locking and wiping, much like the Find My Phone feature. Furthermore, some of these apps can keep an eye out for broader Android security vulnerability exploits, such as Stragefright, and offer protection from malicious emails and rouge websites, which isn’t so easily covered without an anti-virus app.

Wrap up
That’s quite a list, but there are plenty of little things that you can quite easily do to protect your privacy and help keep your Android devices a little more secure. On top of all the apps and settings listed here, perhaps the most effective change that you can make is to tweak your phone habits. Keep location usage to a minimum, disable or uninstall apps that you don’t use, keep an eye on app permissions during updates, and change your passwords regularly, and you should be safe enough.
If you have any of your own privacy tips and tricks, please feel free to share them in the comments below.
Read Next: What are Android app permissions and how to use them if you’re not a developer
Thank you for being part of our community. Read our Comment Policy before posting.