Affiliate links on Android Authority may earn us a commission. Learn more.
Google’s Play Protect service had huge impact on security in 2017
- Play Protect automatically scans Android devices for malicious software. It uses machine learning to identify and remove those apps.
- This relatively new feature was a massive boon to Android security in 2017, according to Google’s annual report.
- However, the best way to stay protected is still to only install apps from the Google Play Store.
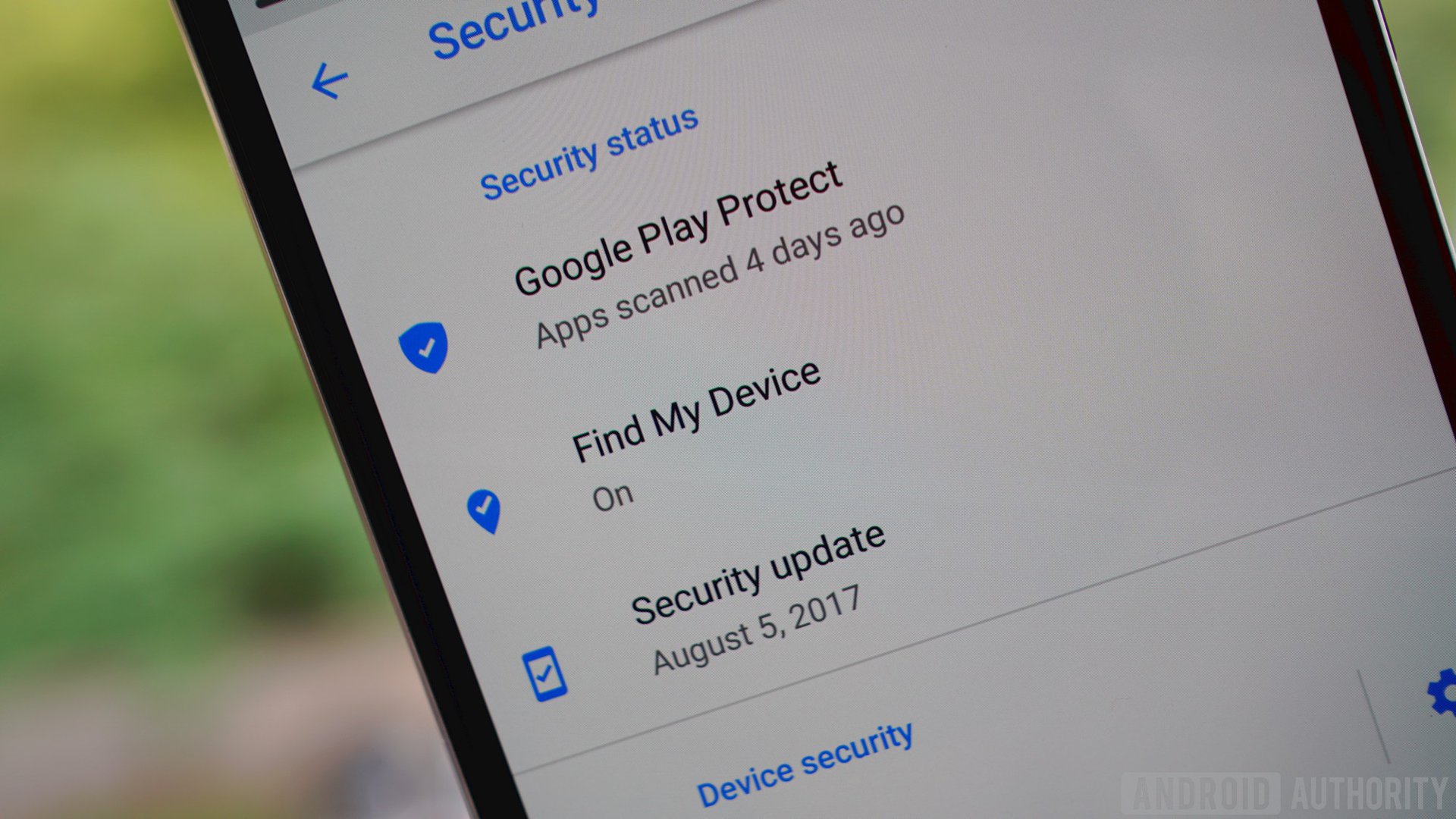
Last year, Google rolled out a new security feature in Android devices: Play Protect. To help combat malicious apps that users either knowingly or unknowingly install on their devices from outside the Google Play Store, Play Protect scans through every Android device (running Android 4.3 Jelly Bean or above) looking for these potentially harmful apps (PHAs) and removes them.
According to Google’s annual Android Security Year in Review report, released today, Play Protect had a considerable impact on neutralizing security threats within Android last year. The feature was responsible for the removal of 39 million “Potentially Harmful Apps” (PHAs). That’s a lot of malicious apps.
Play Protect initially needed a data connection to work, but Google discovered that many PHAs were causing damage while devices were off-the-grid, so to speak. When the company enabled Play Protect to work without a data connection, scanning every device at least once a day for any PHAs, 10 million PHAs were discovered and removed.
The Play Protect software is powered by machine learning, which enables it to scan, identify, and remove PHAs without any human interaction. According to Google, machine learning accounted for just over 60% of the PHAs removed from devices in 2017.
Of course, the absolute best way to prevent malicious software from wreaking havoc on your device is to only install apps from the Google Play Store. Play Protect is undoubtedly an excellent assist if you need an app that’s not available from the official outlet, but you should be downloading apps from Google’s official marketplace whenever possible.
In other security news, Google saw a jump in the number of devices that received after-sale security patches — 30 percent more in 2017 than in 2016. While this is indeed progress, it is worrisome to think that there are still smartphones out there, even flagship models from high-end manufacturers, that are months behind when it comes to security patches.
Google also made note that there were no significant security vulnerabilities in Android last year that weren’t eventually patched. However, it doesn’t really help if Google sends security patches to smartphone manufacturers if those manufacturers don’t then send the patch to the users.
These gripes aren’t really Google’s fault, although the company should be leaning on manufacturers more when it comes to rolling out Android updates to devices. Perhaps some sort of punishment should be admonished if manufacturers don’t push out timely Android security updates to any device less-than two years old? That would at least be a start.
You can read Google’s full, 56-page report here.
Thank you for being part of our community. Read our Comment Policy before posting.