Affiliate links on Android Authority may earn us a commission. Learn more.
Study finds 87% of Android devices are insecure due to lack of security updates

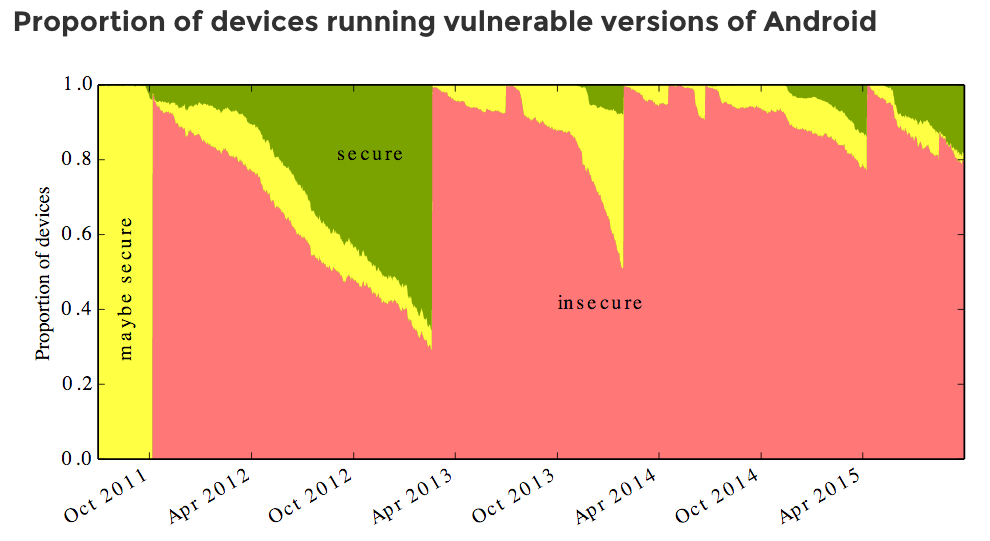
From the Stagefright exploit to other recent security vulnerabilities found in the Android ecosystem, it’s no secret that device security has lately been on the minds of OEMs and consumers alike. A recent study, partially funded by Google and conducted by the University of Cambridge Audio, shows that more Android devices might be more insecure than most of us think. According to a blog post from one of the researchers, Alastair R. Beresford, on average throughout the last four years, a whopping 87% of Android devices are vulnerable to attacks by malicious applications. Beresford says that this is due to device manufacturers not providing security updates on a regular basis. He comments that while some OEMs are much better than others, this is still a major problem.
The researchers collected this data by having approximately 20,000 users download and run their Device Analyzer application, which can be found in the Google Play Store. Thanks to the app collecting data from a wide range of devices, the researchers were able to rank OEMs on the proportion of devices free from critical vulnerabilities, the number of devices running the latest version of Android, and the average number of vulnerabilities the OEM has yet to fix on any device.

So, which smartphone makers are the best at providing regular updates? According to the findings, Google’s Nexus devices scored the highest with a 5.2 out of 10, making them the safest handsets available. LG isn’t too far behind with a score of 4 out of 10, and Motorola ended up scoring a 3.1 out of 10. Samsung, Sony, HTC and Asus have fallen behind with scores ranging from 2.7 down to 2.4.
For a more detailed breakdown of these numbers, head to the recently-launched AndroidVulnerabilities.org.
Google, Samsung and a number of other manufacturers have been doing their part to bring monthly security updates to their range of current Android smartphones. The researchers hope that by quantifying the problem, they’ll be able to help people make a decision when choosing a device. This will, in turn, provide incentive for other OEMs to take regular security updates more seriously.
Thank you for being part of our community. Read our Comment Policy before posting.