Affiliate links on Android Authority may earn us a commission. Learn more.
Hackers can control your smart speakers by shooting laser beams at them

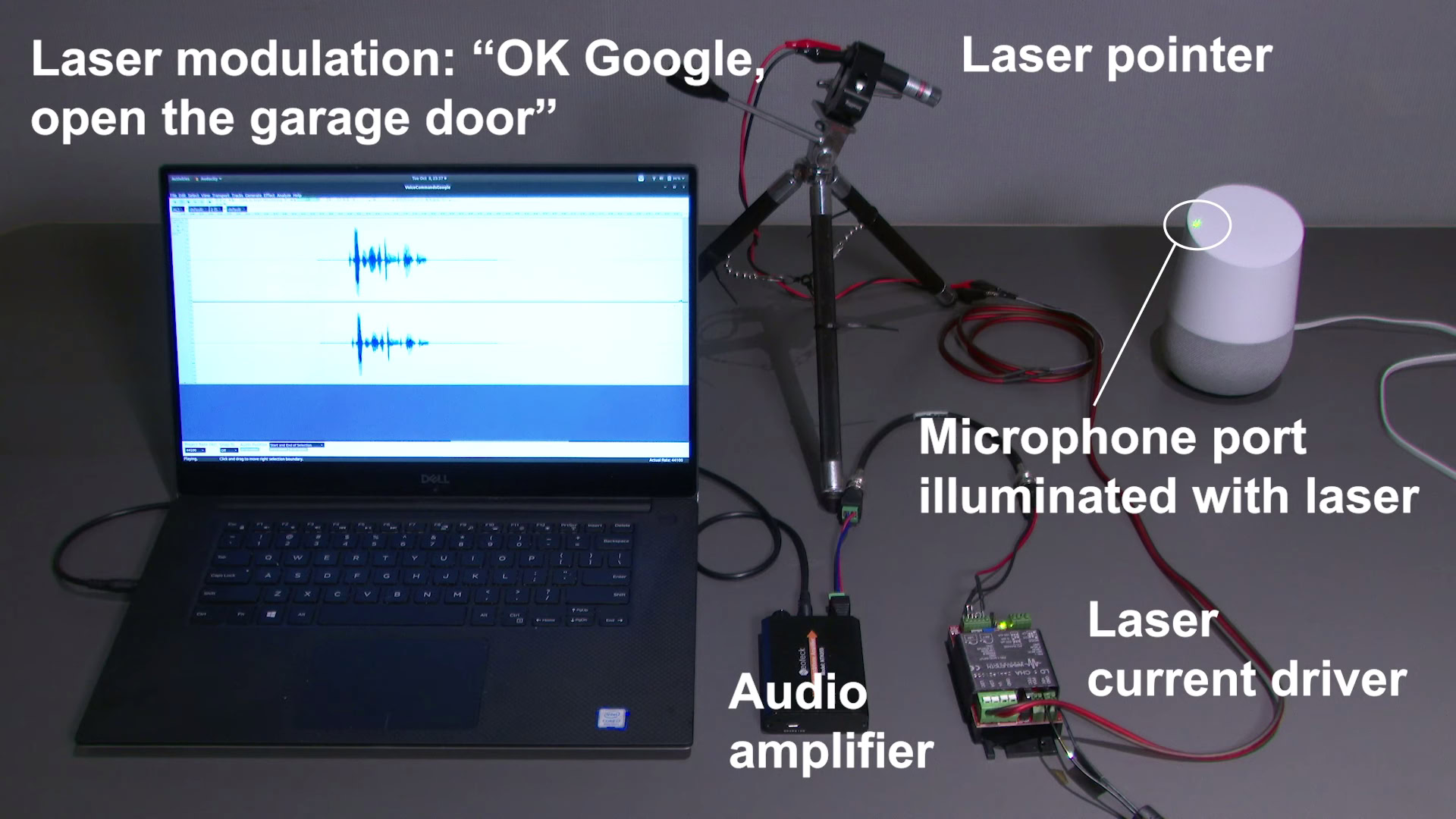
In a series of bizarre experiments conducted by researchers from the University of Michigan and Tokyo’s University of Electro-Communications, smart speakers from Google, Amazon, Facebook, and Apple were hacked using laser beams.
It might sound like something straight out of a sci-fi movie, but all that was needed to remotely control smart speakers was less than $400 worth of equipment. In return, the hacked voice-enabled devices were tricked into opening garage doors and even starting vehicles in some cases.
How does the smart speaker laser hack work?
Since smart home devices are usually placed near doors or windows, attackers can have a clear line of sight for initiating this laser-based attack.
Microphones on smart speakers and even smartphones convert sound into electrical signals. Instead of sound, however, an attacker can encode unauthorised voice commands into a laser light beam.

For the trick to work, the malicious laser needs to hit the microphone on a smart speaker or phone. This remotely causes the microphone to pick up electrical signals representing the attacker’s commands.
For instance, a hacker can use this trick to switch on/off the voice controlled devices in your home or even open your front door remotely.
Researchers were able to send these spiked laser beams and control most smart speakers from a distance of 164 feet. They say it was harder to remotely control voice assistants on phones (both Android and iOS) using the method.
Android phones could only be controlled from a distance of 16 feet, while iPhones could be controlled from 33 feet away.

The researchers are now working with Google, Apple, Amazon and others to mitigate the issue.
A Google spokesperson told Wired that the company is “closely reviewing” the research paper. “Protecting our users is paramount, and we’re always looking at ways to improve the security of our devices,” the spokesperson added.
Thank you for being part of our community. Read our Comment Policy before posting.