Affiliate links on Android Authority may earn us a commission. Learn more.
New Android adware reportedly “nearly impossible” to remove
Lookout has discovered a new form of adware that roots a device after the user installs it, then entrenches itself as a system application. This makes it impervious to any normal means of deleting it, even factory resetting the device.
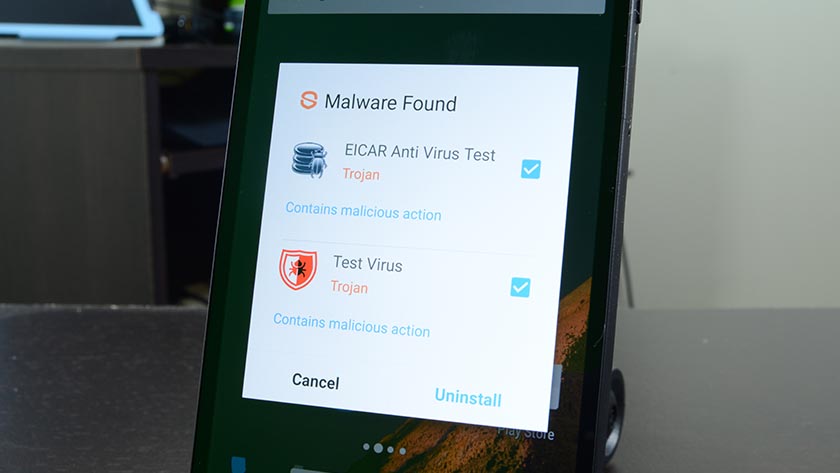
This is a new, more sophisticated version of typical adware, which tends to make itself annoying by constantly pushing ads at the user. Since this form of malware has root access, it doesn’t need to annoy the reader, and most users probably won’t even know they’ve been infected. It’s effectively a family of trojan viruses.
Lookout discovered that this family of trojans hides inside legit apps like Candy Crush, Google Now, Facebook, NYTimes, Okta, Twitter, WhatsApp, Snapchat, and over 20,000 others. Infected versions of these applications are not available on the Google Play store and must be downloaded from third party stores. Since most instances of this malware leave the host app virtually unaltered, users may not notice the sneaky little culprit that snuck in on it.
Lookout reports that successfully embedded instances of this malware are “nearly impossible” to remove, and that the only solution for most users will be to purchase a new phone. Adware with this kind of power is obviously a security risk. Apps typically aren’t given access to files created by other applications, but root access bypasses this safeguard and could expose infected devices to fraud and identity theft.
Lookout has identified three different families of this form of trojan malware: Shuanet, Kemoge (or “ShiftyBug”), and GhostPush. These families have separate designers but share 77% of their code, meaning that even if those responsible for creating them are not working together, they are at the very least aware of each other. The highest rates of infection are in the United States, Germany, Iran, Russia, India, Jamaica, Sudan, Brazil, Mexico, and Indonesia.
So is this really that big of a deal though? While the situation might sound dire, in reality, the odds of being infected by such a trojan probably is pretty low. As already mentioned, these infected apps are found in 3rd party stores, so if you stick to official channels — you should have very little to worry about.
Thank you for being part of our community. Read our Comment Policy before posting.