Affiliate links on Android Authority may earn us a commission. Learn more.
XDA-Developers hackers make booting from SD Card possible for Exynos-based devices
The awesome hackers over at XDA-Developers forums are always at work making tweaks and hacks for our devices. They are one of the biggest reasons why Android devices are so customizable and so much hacking stuff is available for us geeks. Now, a new development described as a “game changer” has been made by members of the forum, which is no less than a breakthrough when it comes to hacking certain Samsung Exynos-based devices including the Galaxy S3 and the Galaxy Camera.
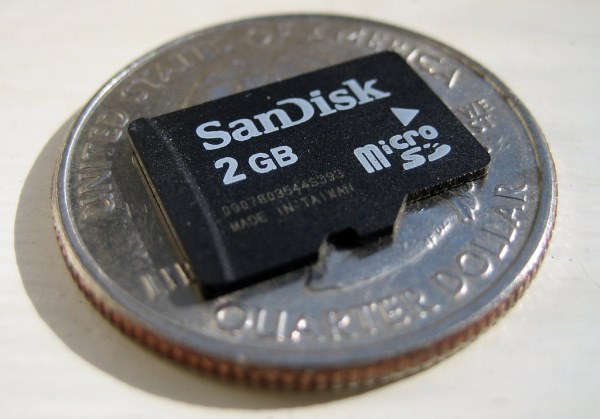
XDA Elite Recognized developers adamoutler and Rebellos have figured out a way to boot these devices from the SD Card. This was not possible until now. The hack would allow users to boot their devices with an open source bootloader and is not like chroot style dual booting.
Thanks to this new hack, developers will be able to get rid of Samsung’s closed source bootloaders and boot directly from the SD card on the mentioned devices. Most importantly hackers will be able to fix brick-bugged Galaxy S3 devices, which will give relief to many users.
In addition to boot Exynos-based Galaxy devices hackers have also been able to make Fastboot work on the Galaxy Camera.
However, there are still some things that need to be taken care of to make these procedure more user-friendly:
1. EMMC Disable hardware mod (can be undone later)
2. UART hookups for debugging and working in fastboot mode.
3. attempting to rework GS3 Ramdisk for SDCard boot.
4. recreating the proper partition structure on a 16 gig.
There are several other things that could be made possible in the future thanks to this mod, including booting alternate operating systems. More development is being made on this project and developers expect to add support for more devices soon while improving it on the existing ones.
You can follow up with all the news related to this hack by going over to the original thread at XDA forums at the second Source link below.