Affiliate links on Android Authority may earn us a commission. Learn more.
It's still possible to bypass Factory Reset Protection on Samsung phones
You may recall a while back when a guy by the name of RootJunky managed to bypass Factory Reset Protection (FRP) on Samsung and LG phones. Well, he’s at it again, this time discovering a new method for bypassing FRP on the recent crop of Galaxy phones including the S6 line, S7 range, the Galaxy Note 5 and even the brand new Note 7.

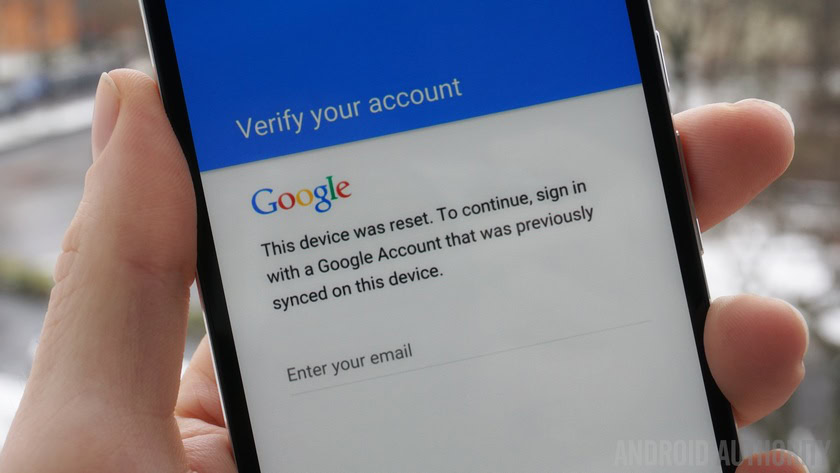
As you probably recall, FRP was a security measure introduced by Google with Android 5.0 Lollipop. Basically, FRP stops someone from stealing your phone and simply factory resetting it by requiring the old username and password associated with the device to be entered before it will successfully boot up again. But as RootJunky has shown on multiple occasions and across multiple devices (including Nexuses), the protection is not foolproof.
The privilege escalation steps involved in this new workaround are rather circuitous – even more so than previous methods – but successfully render FRP useless on a device with the feature enabled. The new method involves connecting to a Wi-Fi network, tethering the device to a computer, installing a program to fake a call to the phone, creating a contact and opting to scan a business card.
Then, using the Galaxy Apps store to install a file manager and then a special app created by RootJunky that serves as a shortcut to the google sign in screen. Once there, he simply creates a new account, reboots and FRP is successfully bypassed, allowing the new user account to set up the device fresh without requiring the old account information to be entered.
The privilege escalation steps involved in this new workaround are rather circuitous, but successfully render FRP useless.
RootJunky admittedly demonstrates a method that could be used by sketchy types to bypass Google’s security on a stolen phone. But it is also massively useful for anyone that has inadvertently bought a second-hand device with FRP enabled and no way to access previous account information. Of course, Samsung and Google will likely be patching the method soon. They should probably just hire this guy while they’re at it.
Do you use FRP? Is Android security a mess?
Thank you for being part of our community. Read our Comment Policy before posting.