Affiliate links on Android Authority may earn us a commission. Learn more.
Anyone can crash your iPhone with this cute little $200 tool
- Flipper Zero is a $200 portable pen-testing tool that can read and emulate a variety of radio waves.
- Bad actors have used the Flipper Zero to send a barrage of Bluetooth requests to nearby iPhones, Android phones, and Windows devices.
- On iOS 17, this can crash the iPhone and lead to a reboot.
iPhones are known for their security, thanks to Apple’s “walled garden” approach that locks down the complete ecosystem. But sometimes, malicious actors don’t want to steal your data; they just want to annoy you. If you’ve recently faced a barrage of random accessory pairing requests on your iPhone and had your phone reboot at the end, someone around you just used a Flipper Zero on you.
What is Flipper Zero?
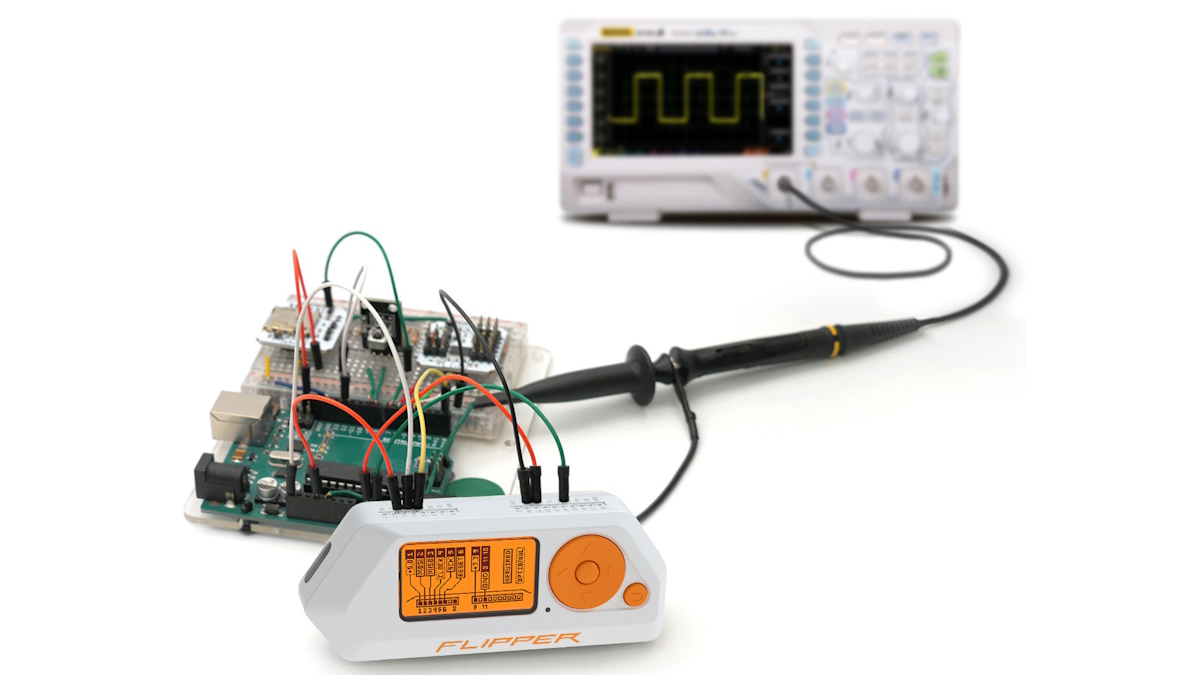
A Flipper Zero is a handy little tool, and at first glance, you will certainly mistake it for a Tamagotchi toy from a decade ago. But this nifty $200 portable pen-testing tool can read and emulate RFID, NFC, Bluetooth, and Wi-Fi. It has a bunch of hardware connection interfaces to connect it to different types of hardware. It has an open-source design, so you can flash it with custom firmware to open it up to new capabilities.
For all the portability Flipper Zero brings in testing a lot of short-range radio frequencies and the like, it also unintentionally lowers the barrier of entry for malicious actors. You can use it to clone some hotel key cards, read RFID chips, and a lot more. It can also be used to crash your iPhone.
How is Flipper Zero being used to crash iPhones on iOS 17
As a report from ArsTechnica highlights, the Flipper Zero with a custom firmware is being used to send a constant stream of Bluetooth messages to nearby iPhones. These Bluetooth broadcasts keep appearing on your iPhone as a pairing request for a Bluetooth accessory. But you cannot pair with an accessory that doesn’t really exist (and you shouldn’t be connecting to unknown devices anyway), so the popup message will constantly disrupt your experience on the iPhone.
By itself, this is annoying. But there’s a dedicated setting labeled as “iOS 17 attack” in the Flipper Zero custom firmware, which then elevates this barrage of Bluetooth requests into crashing and rebooting your iPhone on iOS 17. iPhones on older firmware are not affected, which, ironically, will be a minority as Apple is pretty good with its new iOS version rollouts. The iPhone 15 series is completely affected as it shipped with iOS 17.
What can you do to stop the attack on iOS 17?
If you are the victim of a Bluetooth-based attack like this, you will need to turn off Bluetooth from within the Settings app on iOS 17. Turning off Bluetooth from the Control Centre doesn’t actually completely turn off Bluetooth, so these unwanted Bluetooth notifications will keep coming through if you toggle the setting through the Control Centre.
- On your iPhone or iPad, go to Settings > Bluetooth.
- Turn off Bluetooth.
Unfortunately for iPhone users, there is no way to simply turn off the pairing requests without turning off Bluetooth. Turning off Bluetooth will disconnect you from all of your connected Bluetooth accessories, including AirPods.
Android and Windows are affected too
Android and Windows devices are also susceptible to these Bluetooth request barrages, but it is not immediately clear if you can crash the device eventually.
How to protect yourself from spoofed Bluetooth requests on Android
Android users can protect themselves by turning off scans for nearby devices.
- On your Android phone, go to Settings > Google > Devices and Sharing > Devices.
- Turn off Scan for nearby devices.
Note that disabling this will break your Fast Pair experience, as actual Bluetooth accessories will not immediately pop up on your device. You can still pair them manually the old-fashioned way.
How to protect yourself from spoofed Bluetooth requests on Windows
Windows users can protect themselves by turning off the Swift Pair requests. The same caveat applies, as turning off this setting will break the fast pairing experience. You can still pair accessories manually.
- On your Windows 11 PC, go to Settings > Bluetooth & devices > Devices.
- Scroll down and turn off Show notifications to connect using Swift Pair.
Bluetooth Spoofing attacks are not new, but this makes it easy
Bluetooth spoofing attacks are not new, and there are ways to do it directly from rooted Android phones too. What the Flipper Zero does is make it easy for people to follow a few instructions to become a public annoyance.
We will have to wait for companies to rework their quick pairing mechanisms to avoid such easy exploitation. Until then, consider turning off the settings, as it can become quite difficult to toggle them off if you are actively being attacked. For iPhone users, unfortunately, that is not a practical option.
Update: This article was amended to provide correct instructions for disabling Google’s Fast Pair requests. Thanks to Mishaal Rahman for the correction.
Thank you for being part of our community. Read our Comment Policy before posting.