Affiliate links on Android Authority may earn us a commission. Learn more.
Benchmarks show effect of device encryption on Nexus 6 performance

Nexus devices shipping with Lollipop have full device encryption turned on by default. That’s great from a privacy point of view, but the downside is encryption takes its toll on performance, as benchmarks from AnandTech and direct observations show.
Background
A bit of background: Google has first included the ability to fully encrypt a device on Honeycomb. But that was optional, and most users weren’t even aware of it. However, following the NSA revelations and the growing public awareness of digital privacy issues, Google decided to enable device encryption by default on devices shipping with Lollipop.
Starting with Lollipop, all the data on the device is encrypted by default (with a default password when no password is set, and using the user’s PIN/password/patterns when those are set.) This means the processor must do a bit of extra work each time data is written (encrypted) or read from storage (decrypted).
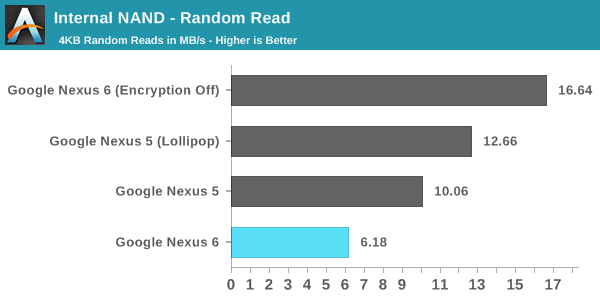
According to benchmarks ran by AnandTech’s Brandon Chester and Joshua Ho the impact of all those cryptographic operations is quite significant. The two ran a benchmark called AndEBench, that is designed to test storage read/write performance, on the Nexus 6 with encryption on (default state), on a modified Nexus 6 with encryption off, as well as on Nexus 5 with Lollipop and Nexus 5 with KitKat.
The difference between the Nexus 6’s storage performance with encryption on and off is massive
The difference between the Nexus 6’s storage performance with encryption on and off is massive: the benchmarks show drops of 62.9% (random read performance), 50.5% (random write performance, and 80.7% (sequential read performance) between the unencrypted Nexus 6 and the encrypted Nexus 6.
To be clear, these benchmarks are specific for storage performance and real life performance is affected by other factors as well. Nevertheless, this performance hit could be noticeable in some cases, especially when the phone works with a lot of data.
Note that when you update to Lollipop, the encryption state remains unchanged, so you shouldn’t worry about it if you’ve just got your OTA on the Nexus 5.
Also worth noting is that this issue affects even users who don’t set a password, PIN, or pattern on their device. That’s because data, as per Google, is encrypted with a default password on first boot, and setting a password simply encrypts the original encryption key.
So what can you do?
There are instructions on XDA that allow you to turn off encryption on a Nexus 6. It involves a bit of work, but if you’re worried about the impact of encryption on your device or just want to have the fastest device possible, it may be worth a look.
Some users on XDA and Reddit are reporting that the change made a noticeable difference for them. As one Redditor put it: “I honestly didn’t think it was that slow before, but seriously, it’s screaming now” (though there could be a placebo component to reports like this one.)
Turning off encryption may also improve battery life, by reducing the workload on the processor.
Keep in mind however that this may not be the cure to the lag/stutter that some Nexus 6 users have reported. AnandTech’s Brandon Chester tested an unencrypted Nexus 6 and he still noticed lag occurring.
Depending on your device, you may not see this issue at all: the Nexus 9 for instance is powered by a different processor and may not behave the same.
Should you even disable encryption?
If you truly care about privacy, it’s probably better and easier to leave your device as is. If you worry about an attacker (be it someone who found your phone, a “commercial” hacker, or a state entity) accessing your private data, an unmodified Nexus 6 with a long password provides the best protection.
If you never secure your device with a PIN, password, or pattern, you’re exposed anyway. If that’s the case, or if you simply don’t care about anyone gaining access to your device data, disabling encryption could result in a better experience. But keep in mind that your results may vary. Plus, there’s a chance a future update will fix these issues.
Thank you for being part of our community. Read our Comment Policy before posting.