Affiliate links on Android Authority may earn us a commission. Learn more.
How to Root the Amazon Kindle Fire
Bring out a new Android device to market, and you can be sure that a method to root it will also come out very shortly after. That was what happened to the Amazon Kindle Fire. Thanks to the Android community of developers and enthusiasts, the Amazon Kindle Fire can be rooted–and fairly easily, too.
The rooting process for the Kindle Fire involves some command line typing, but not the complicated ones though. If you have tried installing a printer for your desktop, then this can be a similar thing. Read on to find out more about how to root your Amazon Kindle Fire.
Things You Need
Step-by-step Procedure
Step 1: Install the Android SDK into your PC. The details about how to install the software development kit will not be discussed here because it’s a totally different subject on its own.
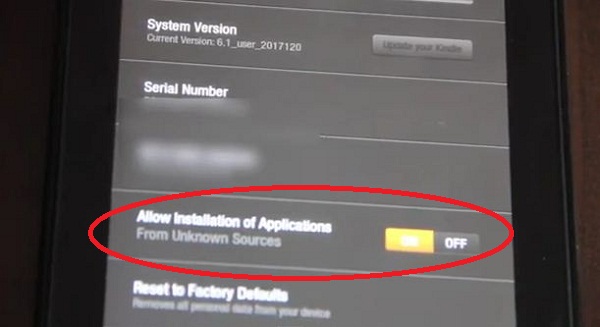
Step 2: You now have to turn on “Allow Installation of Applications From Unknown Sources”. This can be done by tapping the Settings icon at the top right corner. Then, go to More->Device. You can turn on the setting from there.
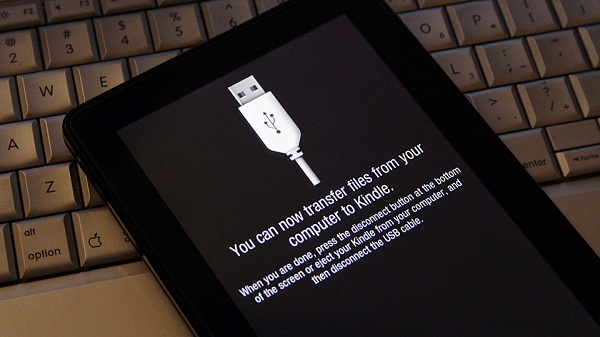
Step 3: Connect the Kindle Fire to your PC using the micro USB to USB cable. If the connect screen comes up on the screen of the Kindle Fire, please do not tap on connect for this will enable USB connection.
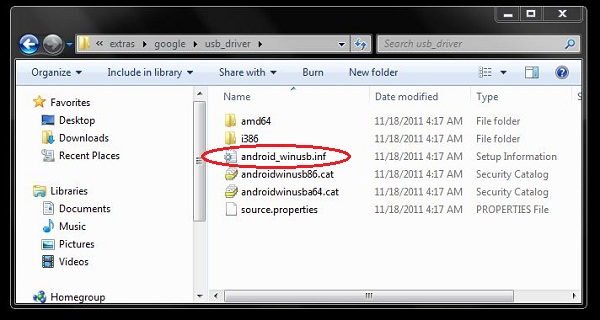
Step 4: Modify android_winusb.inf
- Go to the folder where the SDK is installed.
- Open Extras->Google->USB Driver.
- Right click on android_winusb.inf and choose “Open with” then select Notepad.
[Google.NTx86] and [Google.NTamd64] in the text that you just opened.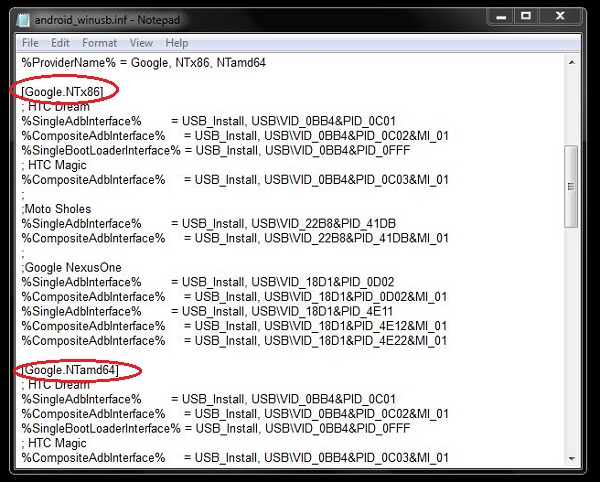
[Google.NTx86] and [Google.NTamd64] line (make sure to save the file after editing):;Kindle Fire
%SingleAdbInterface% = USB_Install, USBVID_1949&PID_0006
%CompositeAdbInterface% = USB_Install, USBVID_1949&PID_0006&MI_01
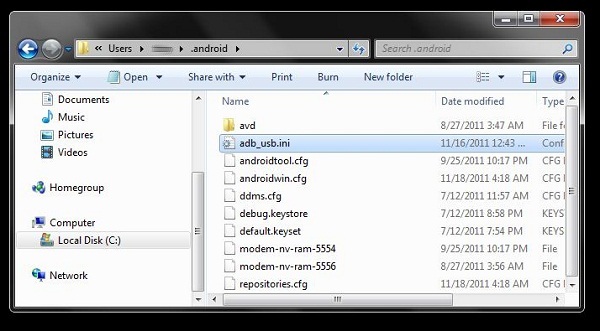
Step 5: Create adb_usb.ini and save it into the .android folder.
- Open Notepad.
- Type
0x1949and then save the file as adb_usb.ini - Open Computer.
- Go to Users.
- Open the user login name folder you are using.
- Copy and paste adb_usb.ini into the
.androidfolder which you will see under the login name folder.
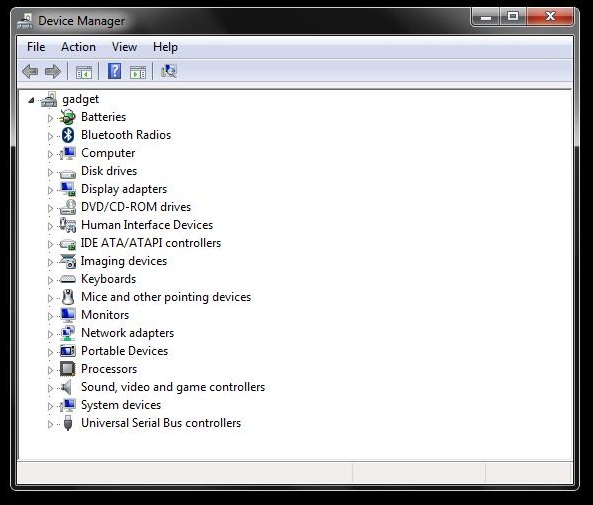
Step 6: Update the USB driver for the Kindle Fire.
- Open Device Manager from the Control Panel window.
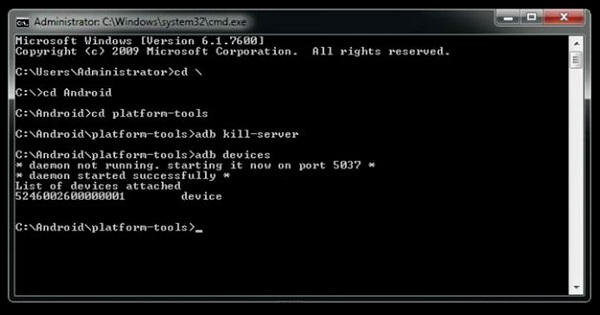
Step 7: Check if Android SDK will now recognize the Kindle Fire.
- Open up a command prompt window.
- Go to the folder were the Android SDK is installed using the
cdcommand. - From the Android SDK folder, access the
platform-toolsfolder by still using thecdcommand. - Under the
platform-toolsfolder, issue theadb kill-servercommand. - Next you have to issue the
adb devicescommand. This will give you text similar to the one below. This will indicate that the SDK recognizes the Kindle Fire.
* daemon not running. starting it now on port 5037 *
* daemon started successfully *
List of devices attached
5246002600000001 device
Step 8: The last part of the process is to root the device. Since we already downloaded the software from Shortfuse, we just have to extract it. After extracting the software, you just have to run it and it will automatically do its charm.
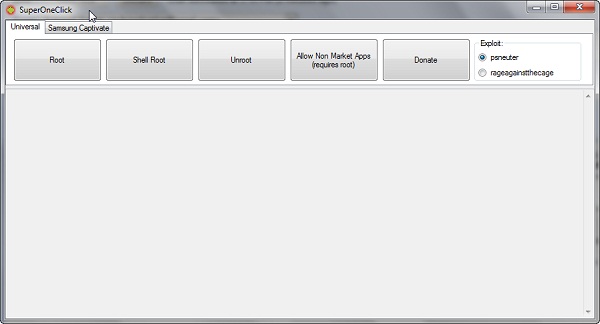
Now that rooting is done, your Kindle Fire will now be open for endless possibilities. More third-party apps can now be installed on the device.
Thank you for being part of our community. Read our Comment Policy before posting.