Affiliate links on Android Authority may earn us a commission. Learn more.
Everything you need to know about Host Card Emulation

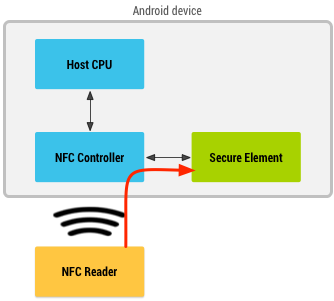
This reliance on the secure element isn’t just a problem in the U.S. In every market where banks want to enable NFC mobile payments there needs to be help from the carriers. This isn’t an ideal solution. One possible answer would be to include the necessary hardware in the actual mobile phones and so by-pass the SIM card. However all this does is move the need for cooperating from the carrier to the handset manufacturer or to the chipset maker.
The U.S. is the last major market to still use the old-fashioned swipe-and-sign system.
A contactless card?
Although the U.S. seems to be ahead of the rest of the world with regards to mobile payments, it has been languishing behind Europe when it comes to alternatives to the traditional swipe and sign system used for card payments. Europe, and other large parts of the world, use smart credit/debit cards with integrated chips. To use them to make a payment the consumer inserts their payment card into a little machine and enters their PIN number. There is no need for a signature and part of the authorization for the payment is granted when the card tells the reader that the PIN number entered is correct. The PIN is actually stored on the card in its secure element. The branding of such systems is different around the world but the technology is essentially the same. In the UK and Ireland it is known as Chip and PIN, in Europe they are often referred to as EMV cards. EMV stands for Europay, MasterCard and Visa, the companies behind the technology. Besides Visa and MasterCard, Diners Club and American Express also support EMV.

“The U.S. is the last major market to still use the old-fashioned swipe-and-sign system, and it’s a big reason why almost half the world’s credit card fraud happens in America, despite the country being home to about a quarter of all credit card transactions,” wrote Tom Gara.
Since the push to catch up with Europe is coming from Visa and Mastercard, it isn’t a surprise that these two payment processing giants are also pushing NFC mobile payments via HCE.
Security
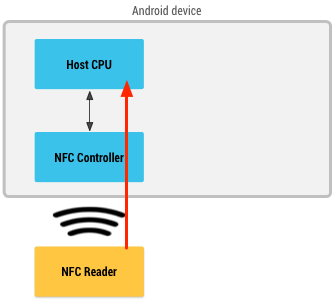
When there is no secure element an Android app must provide the missing functionality and the NFC data is sent directly to the app. Android’s HCE implementation guarantees that any NFC data received by the processing app was actually received directly from the controller. There isn’t a way to spoof a payment app with data from another source.
The problem with this approach is that it means that the smartphone would need to be connected to the Internet at the moment a transaction is authorized. It would also mean that the cloud service would need to reply to the NFC card reader in the sales terminal in less than half a second. These two constraints aren’t practical. Therefore the companies will use payment tokens.
[quote qtext=”MasterCard’s approach combines custom software on the mobile device with highly secure cloud-based processing.” qperson=”Mastercard” qsource=”” qposition=”center”]
These tokens are stored locally on the smartphone but they only authorize the payment app to make a limited number of payments for a limited amount of time , say one day. Once the token expires or reaches its authorized limits then new tokens need to be fetched. The management of these tokens will happen in the background and can happen whenever the user is online, as part of the normal sync process. This means that if somehow the payment process is completely compromised the retrieved information is only good for a limited amount of time and money. In other words a hacker can’t empty your bank account.
[quote qtext=”Visa will deploy several layers of security to protect payment accounts in the cloud, including at the Visa network, application and hardware levels. One-time use data, real-time transaction analysis, payment tokens and device fingerprinting technology make up a multi-layered defense against unauthorized account access. ” qperson=”Visa” qsource=”” qposition=”center”]
One last thing, in case you a worried that someone will walk down a crowded street and secretly perform fraudulent transactions via a hidden NFC card reader, Android turns the NFC controller and the application processor off completely when the screen of the device is turned off. Scanning a phone with the screen off won’t work!
What are your thoughts? Will you use your Android smartphone for NFC mobile payments even without a physical secure element?
Thank you for being part of our community. Read our Comment Policy before posting.