Pages tagged:
Cybersecurity

Android 17 will soon tell you whether your OS is legit
Google says this measure takes aim at cybercriminals.
Hadlee Simons4 hours ago
0

Shimul Sood11 hours ago
0
Google just blocked a zero-day exploit made with AI
Some Galaxy S26 models just received a root exploit (and Magisk)
Hadlee Simons14 hours ago
0

This popular Chrome extension just got flagged for malware
Hadlee SimonsMarch 16, 2026
0

Google takes down massive shady network that was secretly running on millions of Android phones
Adamya SharmaJanuary 29, 2026
0
Don't scan another unknown QR code without running it by this threat detector
Jay BonggoltoJanuary 27, 2026
0

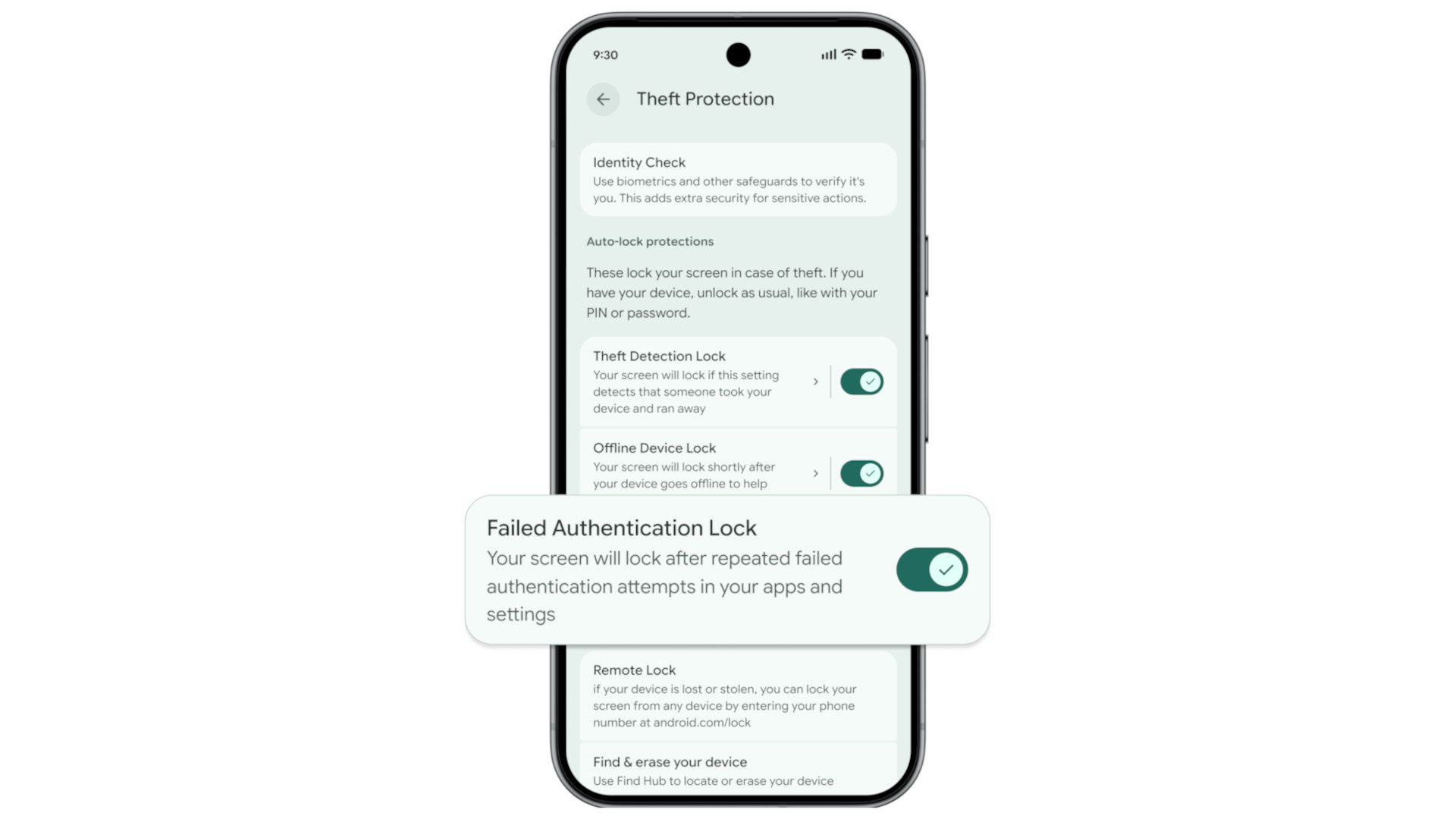
Google just made it even harder for thieves to access your Android device
Hadlee SimonsJanuary 27, 2026
0
PSA: Here's why you shouldn't let strangers with smart glasses use your phone
Hadlee SimonsJanuary 12, 2026
0

Got a random Instagram password reset email? Here's what actually happened
Adamya SharmaJanuary 11, 2026
0

Google's killing off its dark web report because users didn't know what to do with it
Stephen SchenckDecember 15, 2025
0
