Affiliate links on Android Authority may earn us a commission. Learn more.
Smartphones use a second CPU and second operating system in their baseband modems

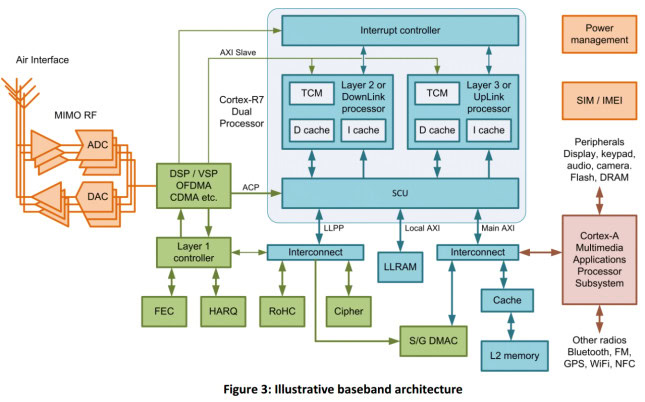
Today’s modern smartphones support a multitude of cellular protocols including GSM, 3G, 4G and 4G LTE. These protocols are complicated and require a significant amount of CPU power to interpret, process and generate the packets which are transmitted to your network provider. This processing is handled by a baseband modem which is a separate chip included in smartphones that communicates with the main processor and sometimes with the phones main memory.
What isn’t often known is that these baseband modems have their own CPUs (often an ARM) and run their own operating system. These small operating systems, which run in these very specific low resource environments, are called Real Time Operating Systems (RTOS) and they are often just a few hundred kilobytes in size and have very small memory requirements. This means that companies like Qualcomm and Infineon, who are the leading baseband modem makers, can create a single chip which includes a low power ARM CPU, some memory and some digital signal processors (DSPs). The CPU in the chip needs to boot up and load the RTOS as well as load the software needed to process the various cellular standards.
Google has a Binaries for Nexus Devices downloads page which hosts binary hardware support files for its Nexus phones. Among these drivers are various binary files to support the GSM components of Nexus phones and tablets that support 3G or 4G. These files are 100 percent proprietary and little is known about them. What this means is that in every Android smartphone is running an open source operating system on top, but deep down in its internals is a proprietary CPU and OS that is a complete mystery to everyone except the baseband modem maker.
Typically a Real-Time Operating System (RTOS) such as Nucleus or ThreadX will provide the control plane code environment.
Security Vulnerabilities
The problem is that like all software there are bugs in the operating systems used by the baseband modem makers. If there are bugs then there are security vulnerabilities. If there are security vulnerabilities then there is a doorway for hackers to get in.
A few years ago security researcher Ralf-Philipp Weinmann presented some finding at a security conference that demonstrated how to use a baseband hack that takes advantage of bugs in the firmware in mobile phone chip-sets by Qualcomm and Infineon Technologies. Weinmann demonstrated a hack for both an iPhone and an Android device by setting up a rogue base transceiver station which he used to send malicious code to the devices and exploited vulnerabilities found in the baseband processors.
Since then little has changed in terms of the openness of these baseband modems. However one thing is sure they are becoming increasingly more complex and in software engineering terms complexity means more bugs and more bugs means more vulnerabilities.
With the recent NSA / Snowden revelations I shouldn’t be surprised if somewhere in the future we find out that governments have been exploiting vulnerabilities in baseband processors to listen to phone conversations and track the whereabouts of persons of interest!
Thank you for being part of our community. Read our Comment Policy before posting.