Affiliate links on Android Authority may earn us a commission. Learn more.
Marriott's Android app reportedly left customers' credit card information open to hackers for years

Marriott, the popular hotel chain, has been in the news recently regarding an attempt to force customers to use expensive Wifi packages controlled by the hotel chain. After being fined $600K, Marriott has been putting up a fight with the FCC to proceed with controlling customers’ Wifi privileges. The hotel chain is yet again holding the spotlight, but this time, it’s in reference to the Marriott Android app. Randy Westergren, a software developer from XDA Developers, has uncovered a vulnerability in the Android app that has apparently left credit card information wide open to hackers for up to four years. The discovery began when Westergren logged into the app, using only his Membership ID number. After further checking, he found that not only was the website fetching reservations with an completely unauthenticated request, but that anyone with a reservation number and a last name could get instant access to canceling reservations, specific addresses and even the last four digits of users’ credit card numbers.
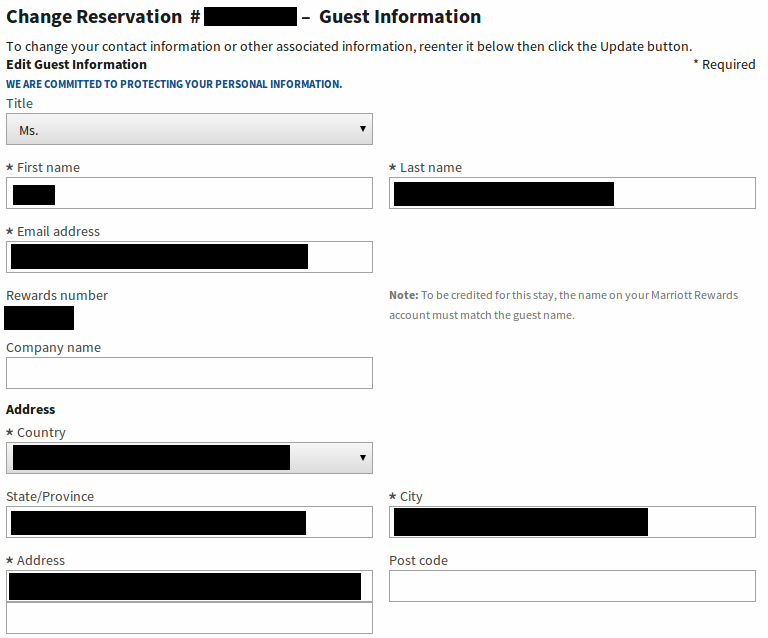
This is the page Westergren was taken to after entering in a reservation number and last name:
We know that the site only provided him with the last four digits of the linked credit cards, but this is enough information for many hackers to work with. He explains further:
You didn’t actually need a rewards number to carry out the attack. The script I wrote actually crawls through all rewards numbers, starting at an arbitrary ID, and stops at the first valid result – a customer with an upcoming reservation. An attacker could have feasibly continued crawling through rewards numbers to fetch all upcoming reservations for all rewards members.
Westergren told Forbes that he “bets the bank” that this vulnerability has been in the app since the launch back in 2011. Marriott’s development team fixed the bug only a day after it came to their attention. Your data should now be safe if you’re a frequent user of the Marriott Android app, though this is still a frightening thought if you’ve ever been a Marriott customer.