Affiliate links on Android Authority may earn us a commission. Learn more.
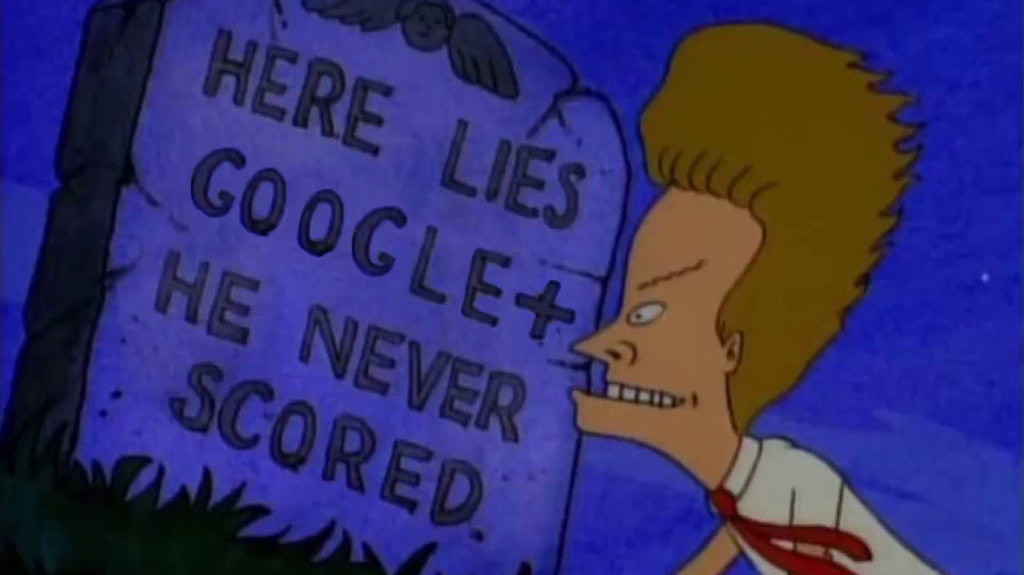
Thanks to a second data leak, Google+ will shut down sooner than anticipated

- Google moved up Google+’s shut-down from August 2019 to April 2019.
- The expedited expiration date is due to a second vulnerability that impacted 52.5 million users.
- The vulnerability possible exposed profile information to developers.
Google announced it has found a second vulnerability in Google+. As a result, the Google+ shut-down has been moved up from August 2019 to April 2019.
The new vulnerability was found in a software update introduced in November and affected a Google+ API. The vulnerability possibly exposed profile information like names, email addresses, occupations, and ages to developers.
The bug impacted approximately 52.5 million users and possibly exposed the aforementioned profile information even when the information was set to not-public. Apps could also access the aforementioned profile information that was shared with another user but was not shared publicly.
Google said it encountered the bug as part of its “standard and ongoing testing procedures” and fixed it within a week of its discovery. Google also said its systems were not compromised and had no evidence that developers with profile information access were either aware of it or abused it.
Regardless, Google notified impacted users and enterprise customers. The company also said it will shut down API access to Google+ within the next 90 days.
A similar vulnerability led to Google+’s demise in the first place. Disclosed in October but discovered in March, the vulnerability exposed private user data to developers for three years. Google said no developer was aware of the bug or misused the affected Google+ API.
Google failed to disclose the issue immediately due to “fears that doing so would draw regulatory scrutiny and cause reputational damage.” Thankfully, Google did not wait eight months to disclose Google+’s second vulnerability.
Thank you for being part of our community. Read our Comment Policy before posting.