Affiliate links on Android Authority may earn us a commission. Learn more.
Factory Reset Protection can be easily bypassed on Android N and unpatched stock Marshmallow
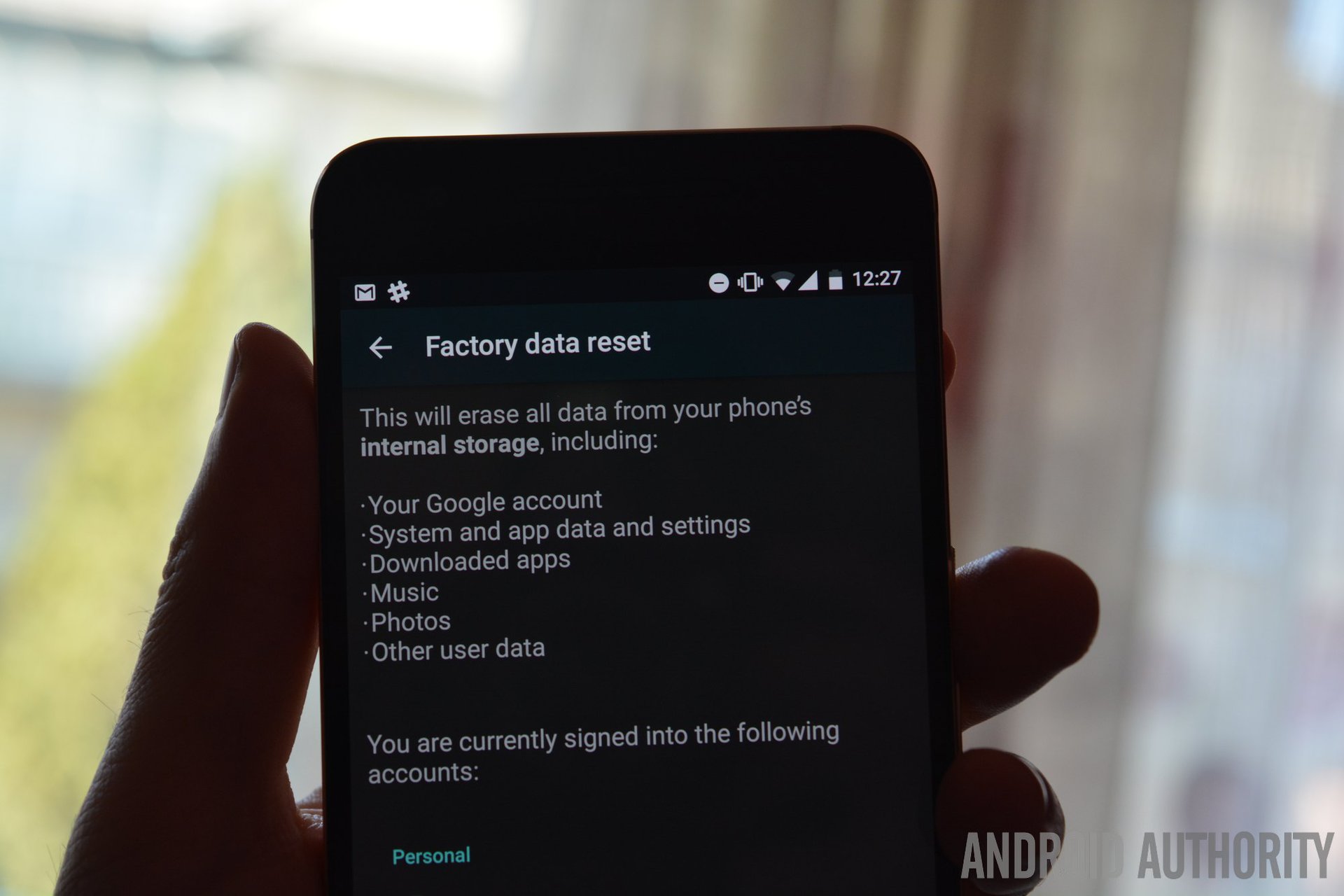
Factory Reset Protection (FRP), a protection measure that’s supposed to prevent thieves from using stolen Android devices, is easy to bypass on some Nexus devices running on unpatched versions of stock Marshmallow or even Android N preview.
In case you’re not familiar with FRP, here’s how it works: if a device that has a Google account associated to it is reset to factory settings, FRP will ask for the credentials of that Google account before the system loads up.
In theory, if someone steals your device, the thief won’t be able to just reset it and go on their merry way using it, because they don’t know your Google account password.
In practice, at least until the March security update, it was simple to bypass FRP. The method, discovered by RootJunky, involves just a few simple steps that anyone can follow, even without any knowledge of Android. It’s a basic exploit of security holes in Google’s keyboard, dialer, and messaging apps and the OS itself. Here’s a video showing how to bypass FRP on a Nexus 6P:
Now, it appeared that Google had patched the issue in the January security update. It did not – earlier this week, I used this exploit to get into a Nexus 6P (running on the February patch) that had accidentally remained locked to one of my colleagues’ Google accounts.
Instead of asking for their personal Google credentials, I decided to give this video a shot, and, sure enough, it worked – I managed to get into the device, activate developer options, make the bootloader unlockable, and reset the device. I removed my colleague’s account and entered mine, like FRP didn’t even exist.
I wasn’t able to test whether the hole was patched in the March update, but the security bulletin mentions an “Elevation of Privilege Vulnerability in Setup Wizard” issue described as follows:
A vulnerability in the Setup Wizard could enable an attacker who had physical access to the device to gain access to device settings and perform a manual device reset. This issue is rated as Moderate severity because it could be used to improperly work around the factory reset protection.
That sounds a lot like this problem. Then again, three issues with the same description were marked as fixed in the February and January updates, and I was still able to bypass FRP.
A similar exploit exists for Android N preview – RootJunky published this video showing the steps required to bypass FRP on a Nexus 6P with Android N. The procedure involves a few more steps, but it’s so simple that even a seven-year-old could follow.
This is clearly a serious issue with Factory Reset Protection. If phone thieves with no technical skills can bypass FRP, it negates the entire purpose of the feature, theft deterrence.
The good news is that, thanks to monthly security patches, issues like this can be fixed relatively quickly. The bad news is, it didn’t take RootJunky much to find a different path around FRP and that makes me wonder how secure the whole system is. And security patches only protect people who actively install them in the first place. Outside our Android bubble, people tend to ignore update notifications for weeks, and that’s assuming they even get them on their devices.
Thank you for being part of our community. Read our Comment Policy before posting.