Affiliate links on Android Authority may earn us a commission. Learn more.
What is encryption? Here's everything you need to know
Encryption is a term that many of us have come across, but what does it mean? To put it simply, encryption is the encoding of information. Various online services use it to keep your data private and safe: from text messages and emails to banking details, cloud files, and more.
This article will explore the different types of encryption, how it protects your data, and why it matters. Let’s get into it.
Related: The best VPNs to send your money on
What is encryption?
Encryption is not an invention of the digital age. History buffs will know that cryptography dates back to as early as Ancient Egypt. In ancient times, people used to encrypt secret messages using symbol replacement. The famous Caesar cipher, for example, replaced one letter with another a fixed number of spaces down the alphabet.
Today, the basic principle remains the same. Digital encryption takes readable text (also known as plaintext) and scrambles it. It uses encryption algorithms to achieve this, which are much more complex and powerful than their single-alphabet substitution ancestor.
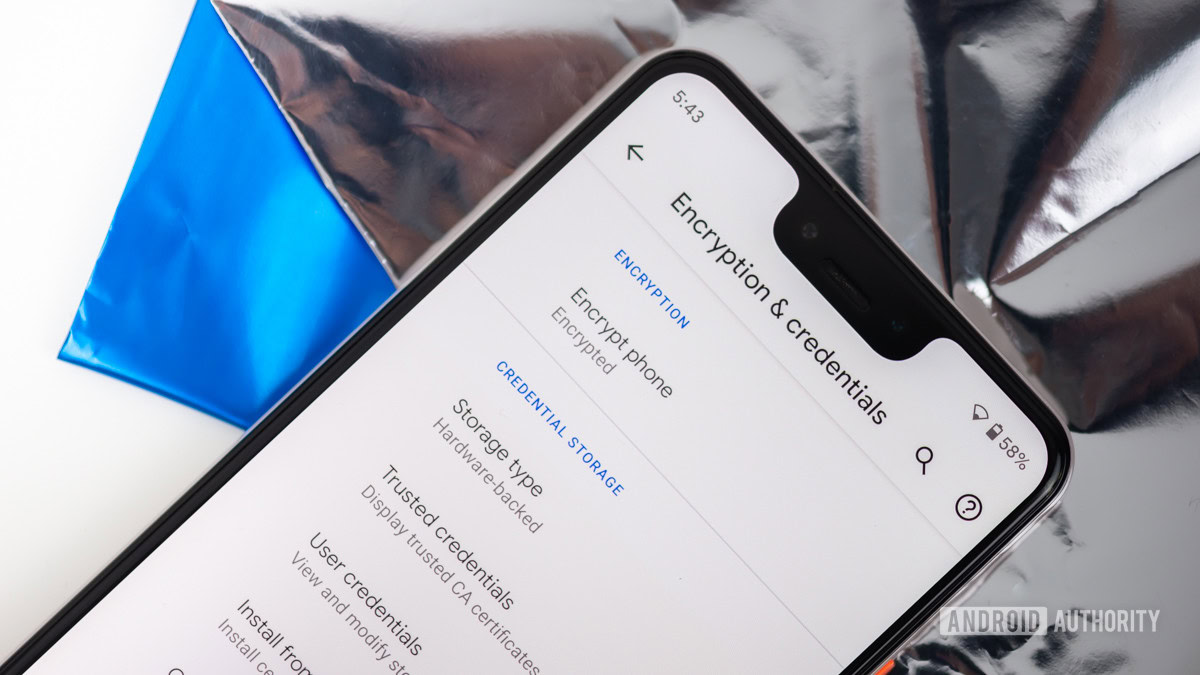
Don’t miss: How to encrypt your Android device
We have variables, also known as keys, to thank for that. They are randomly generated and unique. Some systems even generate new keys for every session. This means that if an attacker wants to steal your credit card information, they will have to know what algorithm encrypts the data and what key. This is not an easy task, as encryption is very resistant to brute force attacks. It’s also why it is one of the best ways to protect your sensitive data online.
Types of encryption

There are two main types of encryption: symmetric and asymmetric. The main difference between them lies in their use of keys.
Symmetric encryption utilizes a single key which both communicating parties use for encryption and decryption. However, both devices need to have the key before the communication begins.
Related: Can your ISP see your browsing history? Here’s what you need to know
On the other hand, asymmetric or public-key encryption opts for a two-key approach. One key is private, and the other is public, hence the name. The private key is only known to your device, but your phone or PC will send the public key to devices it wants to communicate with securely. The receiving device needs its private key and the public one to decode the encrypted data. This is why you shouldn’t worry about the “public” name. No one can access your information without the necessary private key.
Encryption algorithms
As previously mentioned, there also are various algorithms that can use symmetric or asymmetric encryption. Here are five of the most commonly used encryption algorithms and how they work:
- AES — The Advanced Encryption Standard is one of the most secure symmetric encryption algorithms. It uses ciphers with 128-bit block sizes and key lengths of 128, 192, or 256 bits. AES is the algorithm of choice for multiple organizations, including the US government.
- Triple DES — When the original Data Encryption Standard (DES) became susceptible to attacks, it was replaced by Triple DES. Its name is derived from its use of three 56-bit keys. It’s a symmetric encryption algorithm, but it has fallen out of fashion in recent years with the emergence of more secure options like AES.
- Blowfish — Security expert Bruce Schneier invented this encryption algorithm. Like Triple DES, it emerged to replace the outdated DES. It is a symmetric-key block cipher that ranks among the most secure algorithms. It can be used by anyone thanks to its public domain status.
- Twofish — Another invention of Bruce Schneier, TwoFish is the more advanced successor of Blowfish. It is a symmetric encryption algorithm that uses keys up to 256 bits in length. It is not only fast and secure, but it’s in the public domain, just like its predecessor.
- RSA — An asymmetric encryption algorithm, RSA is one of the oldest and most widely used standards for data encryption online. It is relatively slow, but it is regarded as very secure.
What is it used for?
Now that you know what encryption is and how it works, you may be wondering what it’s used for. As previously mentioned, encryption is essential for a private and secure online experience. Whether you are sending an email, shopping online, chatting with friends, or uploading files to the cloud, sensitive information needs to be protected.
Even if you might not be aware of it, many of the online services you use already employ some form of encryption. Here are some common encryption uses and how they work.
End-to-end encryption

Due to its increasing popularity in recent years, you have probably heard of end-to-end encryption. So, how does it work? Typically, much of the information you send online passes through and is stored by third parties, including your email provider. Even if the data is encrypted, that usually only happens while in transit. Once your email arrives at its destination, it often doesn’t have the same level of protection.
Related: The best encrypted private messenger apps for Android
The same doesn’t apply with end-to-end encryption, also known as E2EE. End-to-end encryption makes information readable only to the communicating parties. Not even your ISP or email provider are given ways to decrypt it. This makes it great for the privacy-conscious and those concerned with security. Of course, E2EE is not 100% foolproof, but it’s much better than most alternatives.
A number of popular messaging services and email providers such as Signal, WhatsApp, and Proton Mail already use end-to-end encryption.
HTTPS

If you want your browsing habits and data to remain private and secure, you should familiarize yourself with HTTPS. This protocol is used on the Internet. You can identify it by the padlock icon in the corner of your browser’s address bar. It provides secure communication via TLS (Transport Layer Security) or SSL (Secure Sockets Layer) encryption.
HTTPS authenticates your connection by requesting a digital or public key certificate signed by a trusted third party. However, unlike end-to-end encryption, HTTPS generally protects your data while in transit. This means it is less private comparatively, but it’s still a must-have for anyone that wants to protect their online data.
Read next: The best privacy browsers for Android
The easiest way to ensure that your web communication uses HTTPS is by installing a browser add-on such as HTTPS Everywhere. It is available for all major browsers such as Chrome, Firefox, Opera, and even Firefox for Android.
Cloud storage encryption

Storing photos, videos, and documents on the cloud is more common than ever. This necessitates the use of encryption to protect sensitive files. Many cloud storage providers offer some form of it.
There are three types of data cloud providers have to deal with: data-at-rest, data-in-transit, and data-in-use. Their names are pretty self-explanatory. The first is data that is stored and not currently in use. Data-in-transit is information sent to one or multiple parties, while data-in-use is often utilized by applications, which makes it difficult to encrypt.
Read next: Best free cloud storage
However, whether any of this data is encrypted depends on your provider. Some may offer both data-at-rest and data-in-transit encryption, while others may only encrypt sensitive data. The types of encryption also vary from provider to provider. Unfortunately, E2EE is still not very common in the cloud space.
Not many cloud storage services offer end-to-end encryption.
Nevertheless, most popular services provide TSL/SSL encryption for data-in-transit and some form of encryption for data-at-rest files. Some like Dropbox, for example, also offer end-to-end encryption tools like Boxcryptor. They can encrypt your files locally before uploading them to the cloud.
Disk encryption

If you want to take your protection to the next level, you might want to protect files saved on your PC too. This is where disk encryption comes in. It allows you to encrypt your hard drive, thereby securing everything stored on it.
There are a couple of ways to go about disk encryption: using software or hardware. With the latter, you’d need a self-encrypting drive. It encrypts and decrypts data automatically, making it one of the easiest and most worry-free ways to keep your files secure. Various manufacturers, including Samsung, Seagate, Toshiba, and others offer self-encrypting drives (both SSDs and HDDs). However, they usually command high prices.
If you want to save some money, you can use software to encrypt your existing drive. There are many solutions to choose from, but you need to know a couple of things first. Disk encryption software typically uses real-time encryption, also known as on-the-fly-encryption (OTFE). This means that data is encrypted and decrypted as it is loaded and saved. Depending on the software you use, this might result in slower performance. Nevertheless, it might be worth it for those that place security first. Software like BitLocker, for example, uses the AES encryption algorithm with 128 or 256-bit keys, making it a great choice for those that value security and privacy.
Why encryption matters

You have nothing to fear if you have nothing to hide, right? Well, that’s certainly what many people think, but data is big business nowadays. Even if you don’t mind someone knowing about your browsing or shopping habits, you don’t want to have credit card information or private photos stolen. This is why encryption matters. Here are its main benefits:
- Privacy — Some conversations, be they personal or work-related, should stay safe from prying eyes. The same can apply to photos, videos, documents, etc. Encryption is an essential tool if you want to keep these to yourself and intended recipients only.
- Security — Because of the current pandemic, we have to do many things that require inputting sensitive information online. No one wants to have their credit card information or identity stolen while shopping or submitting tax documents.
Of course, encryption cannot protect you from 100% of attacks. It has flaws and limitations, but you will be at a higher risk of exposing yourself to sleuthing and data harvesting without it.
Frequently asked questions
Q: How secure is encryption?
A: Encryption makes your online experience much more private and secure, but it isn’t foolproof. The level of security also depends on the type of encryption used. Nevertheless, it can’t protect you from all online threats. Weak passwords and data breaches, for example, can still result in your information being stolen.
Q: Can encrypted data be hacked?
A: Yes, you can decode encrypted data. However, decryption requires a lot of time and resources. Encrypted data is usually “hacked” with stolen keys instead.
Q: Can encrypted data be encrypted again?
A: Yes, multiple encryption exists. It can use the same or different algorithms, but it is not too common. Most modern ciphers are very hard to crack with brute force attacks without needing a second layer.
Q: What is the highest level of encryption?
A: AES 256-bit is considered the strongest encryption standard. The US government has used AES (Advanced Encryption Standard) since 2001, and many businesses have adopted it since too.
Q: Which messaging apps use end-to-end encryption?
A: Signal, WhatsApp, and iMessage use end-to-end encryption by default. However, other popular apps like Telegram offer it too but only in secret or private chats.
Thank you for being part of our community. Read our Comment Policy before posting.