Affiliate links on Android Authority may earn us a commission. Learn more.
The massive Collection #1 data breach: What is it and what should you do?
- Have I Been Pwned creator Troy Hunt announced the Collection #1 data breach.
- The collection of files contains millions of compromised email addresses and passwords.
- The compromised data supposedly comes from 2,000 databases.
Data breaches have become so commonplace nowadays that we’ve almost become numb to them. However, security researcher and Have I Been Pwned creator Troy Hunt just reported a data breach that will hurt for a long time: Collection #1.
Collection #1 is a massive file that was recently uploaded to cloud storage service Mega. The file features 12,000 separate files that contain 87GB of data.
What’s in the data, you might ask? 772,904,991 unique email addresses and 21,222,975 unique passwords. A significant issue is the stolen passwords having cracked protective hashing. That’s why the passwords show up as plain text instead of being cryptographically hashed when the websites were breached.
Now emailing 768,253 individuals who subscribed for notifications and another 39,923 who are monitoring domains…— Troy Hunt (@troyhunt) January 16, 2019
These cracked passwords allow for a second issue, a practice called credential stuffing. Credential stuffing is when breached username or email/password combinations are then used to get into someone else’s account. Attackers don’t need to brute force or guess passwords — they can just automate the logins.
Credential stuffing is particularly concerning for those that use the same username and password combination across websites.

It just so happens that Collection #1 contains almost 2.7 billion combinations. It also just so happens that roughly 140 million email addresses and 10 million passwords from Collection #1 are new to the Have I Been Pwned database.
Let’s also not forget the decentralized nature of Collection #1. Previous breaches usually had a common silver lining: each breach could be tied down to one website. Not so with this breach, which comprises of breaches across 2,000 databases.
In this case, the only possible silver lining is that Hunt doesn’t know if every single breach in Collection #1 is legitimate. However, Hunt also said that this is “the single largest breach ever to be loaded into HIBP.”
What should I do?
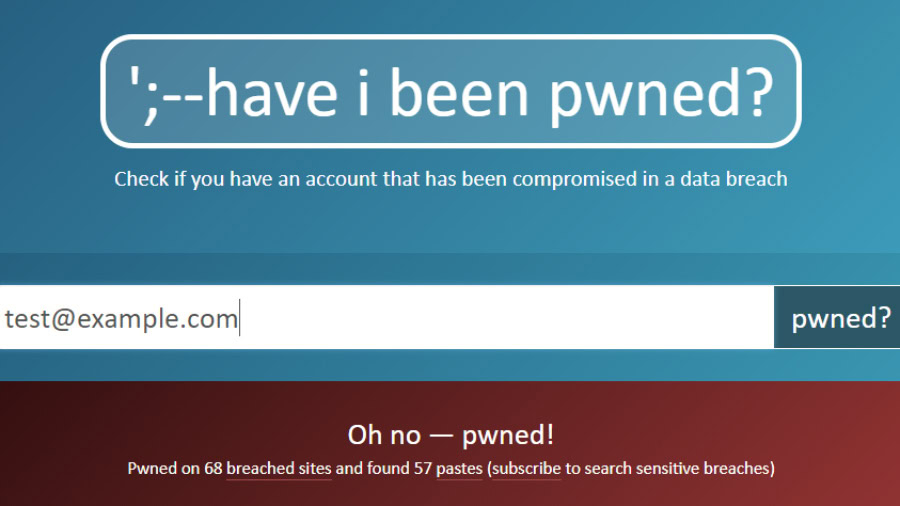
First, go to Have I Been Pwned and type in your email address. The site lets you know if an account that uses that email address was compromised.
If you already used Have I Been Pwned, you should have received a notification of the breach. Almost half of the site’s users are caught up in the breach, so keep that in mind if you’re a member.
From there, click the Passwords tab on the top of Have I Been Pwned. Pwned Passwords lets you know if your password was compromised and helps you to use strong passwords.
If you have a compromised email address and compromised passwords, it’s time to clean up your password practices. If a site supports it, use two-factor authentication. It might not be foolproof, but two-factor authentication helps to dissuade most that might want access to your account.
You can also avoid using the same password across multiple sites. It’s tempting to use the same password for the sake of convenience, but the practice is a dangerous double-edged sword.
Finally, use a password manager. 1Password, Dashlane, and LastPass are three of the more popular options out there, though you can also use the tried-and-true method of pen and paper.
Oh, and change your password. Definitely change your password. Make it something complex, something that can’t be found in a dictionary.
Thank you for being part of our community. Read our Comment Policy before posting.