Affiliate links on Android Authority may earn us a commission. Learn more.
Popular app Airdroid is riddled with security holes (update: patch coming within 2 weeks)
Update: AirDroid’s team has now officially responded with a bit of background on the claimed issues, as well as a promise that it is addressing this issue right now, and will deliver a patch within the next two weeks. You can read the official post here.
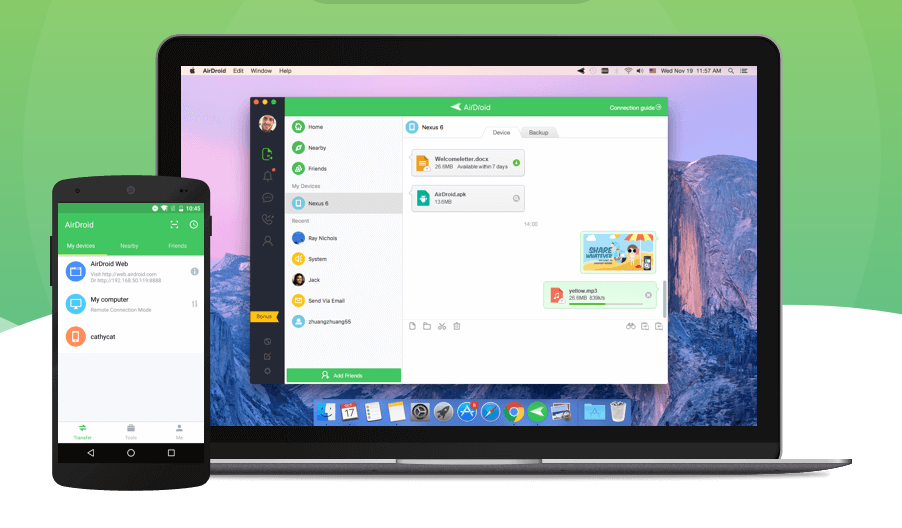
AirDroid is a popular remote access management tool for Android devices that allows you to check the latest notifications, send and receive messages, and access files directly from your computer. According to the data on Google Play, the app has been downloaded between 10 and 50 million times.
But despite being useful as well as popular, it does have a major problem. Back in May, the security company Zimperium discovered a number of security issues in AirDroid. And although the developer has acknowledged them, the issues are still present in the latest version of the app, six months later.
According to Zimperium, an attacker on the same network would be able to intercept the request check for add-on updates and send a malicious, fraudulent APK to the user’s device. In addition, the attacker could also gain full access to the device and see user sensitive data including, among others, the email address and passwords.

In the official report posted on its website, Zimperium wrote, “AirDroid relies on insecure communication channels in order to send the same data used to authenticate the device to their statistics server. Such requests are encrypted with DES (ECB mode) however, the encryption key is hardcoded inside the application itself (thus known to an attacker). Any malicious party on the same network of the target device could execute a man in the middle attack in order to obtain authentication credentials and impersonate the user for further requests.”
It’s sad to see that the developer hasn’t fixed this major security issue despite knowing about it for around six months. Security should be a priority for every developer. Let’s just hope that it will be sorted out with the next update. Until then, we advise you to stop or at least limit the use of the app. Safety first.
Thank you for being part of our community. Read our Comment Policy before posting.