Affiliate links on Android Authority may earn us a commission. Learn more.
Here's how Project Treble will improve security in Android
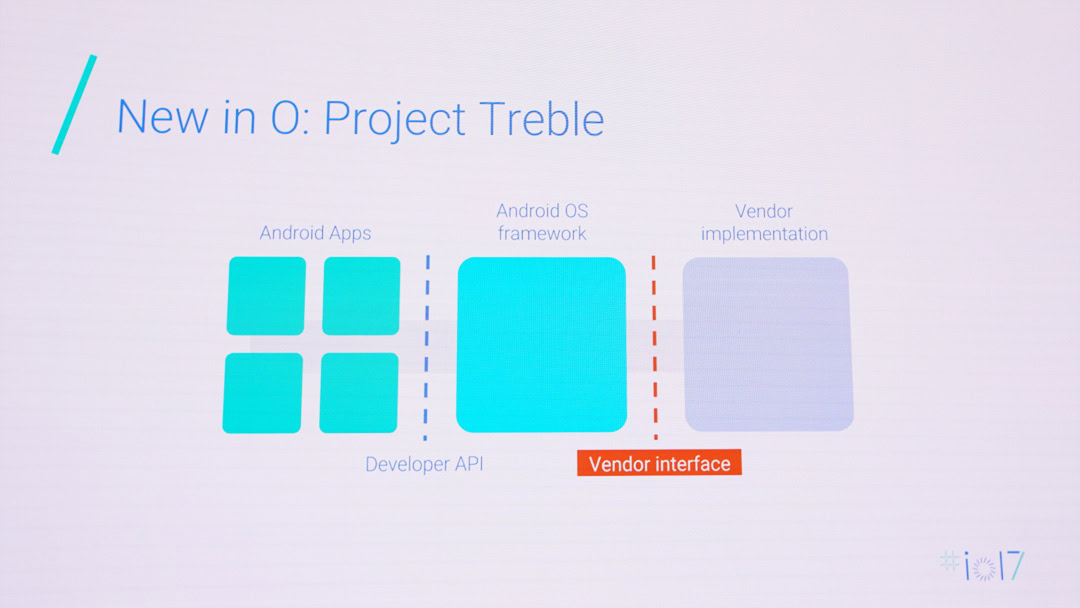
Good news: Android O is about to get a lot more secure thanks to Project Treble, which you may remember as the initiative that will deliver upcoming Android updates in a more timely manner. But Project Treble – which modularizes Android updates into a platform (Google) and vendor (OEM) structure – not only allows essential framework updates to be rolled out faster, it also provides the basis for a more secure Android.

Project Treble does this by extending the principle of least privilege introduced in Android Nougat’s hardening of the media stack. In Nougat, the vulnerable media server (which lay at the heart of the Stagefright exploit) was split into multiple discrete components, so rather than an all-together media server with direct access to audio and video hardware, we instead got a dedicated audio server, camera server and so on, making the entire system less vulnerable.
In Android O, that sandboxing work continues. The Android Developer’s latest blog post details how most direct hardware access has now been removed from the audio and camera servers entirely. By moving various HALs (Hardware Abstraction Layers) from running in a shared process to running in their own sandboxed processes, Google can effectively isolate access to permissions and drivers to only that HAL that specifically needs them.
Previously, all HALs had access to all drivers and permissions because they all lived in the same process. If all of this sounds a little too much like techno babble for you, think of it in terms of Get Smart. The old system would have Maxwell Smart sharing sensitive information with Agent 99 in a room full of eavesdropping KAOS agents. The new process has the cone of silence dropped around their 1:1 conversation, limiting the interaction to a need-to-know basis.
As Google notes, “De-privileging system server and the media frameworks is important because they interact directly with installed apps. Removing direct access to hardware drivers makes bugs difficult to reach and adds another layer of defense to Android’s security model.” Ultimately what all this means is that Google is making security in Android O more granular and specific, isolating the most tempting parts of the system from attackers and shoring up access to non-essential drivers and permissions.