Affiliate links on Android Authority may earn us a commission. Learn more.
Google details malware that turned Android phones into powerful espionage tools
A post on the Android Developers blog discussing the Chrysaor malware for Android has left me feeling a mixture of amazed and afraid.
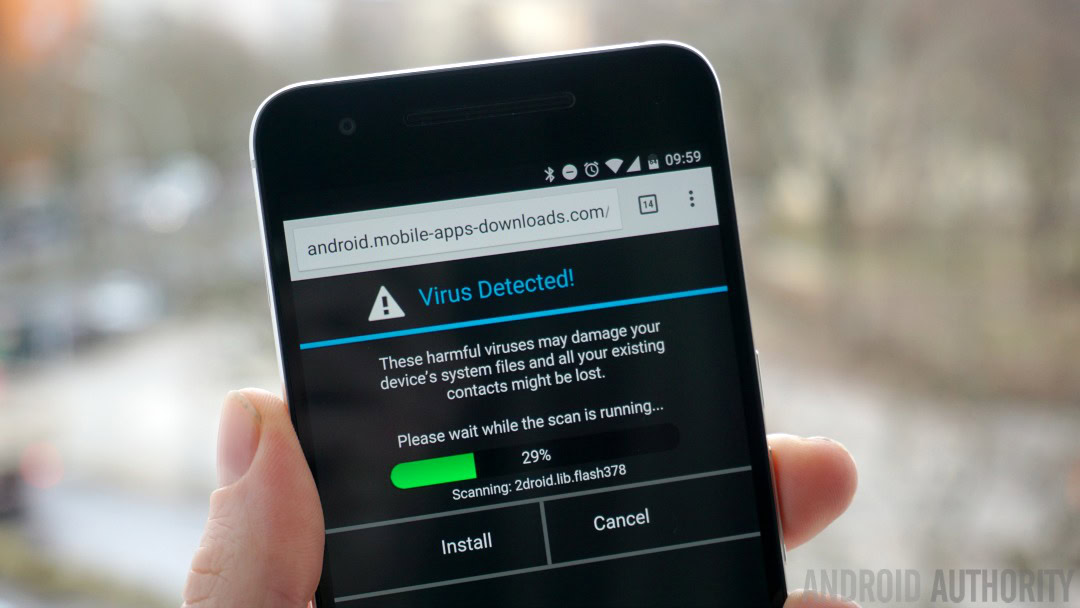
Discovered late last year, Chrysaor is spyware believed to have been created by NSO Group Technologies, an Israel-based group which specializes in the development and sale of software exploits. It’s thought to be a descendant of the Pegasus spyware previously found on iOS, and made its way onto handsets through apps which weren’t available in the Google Play Store.
According to a report from security firm Lookout, Pegasus and its Android counterpart Chrysaor appear to be spying tools deployed by “nation states and nation-state-like groups.” In other words, spies.
“Usually, PHA [potentially harmful app] authors attempt to install their harmful apps on as many devices as possible,” wrote some of Android’s security team on the Developers blog. “However, a few PHA authors spend substantial effort, time, and money to create and install their harmful app on one or a very small number of devices. This is known as a targeted attack.”
The Android team says it has discovered Chrysaor on less than three dozen Android devices in total, and this, combined with the sophistication of the app’s capabilities (outlined below) indicates that the malware was used more as a tool for spies than as way to cajole money out of consumers.
Here’s some of the things that Chrysaor capable of:
- Data collection: collects user data including, SMS settings, SMS messages, Call logs, Browser History, Calendar, Contacts, Emails, and messages from selected messaging apps, including WhatsApp, Twitter, Facebook, Kakoa, Viber, and Skype.
- Screenshots: captures an image of your current screen.
- Keylogging: records what you type.
- RoomTap: this “silently answers a telephone call and stays connected in the background, allowing the caller to hear conversations within the range of the phone’s microphone.” If the user then unlocks their device, they are greeted with a black screen while to spyware drops the call and resets the call settings. As suggested above, this isn’t really a feature that’s of use to typical malware creators.
What’s possibly even more impressive/frightening is that Chrysaor can remove itself from a device if it becomes compromised — it can basically self-destruct.
If the app fails to interact with the Google server after 60 days, for example, indicating that it has been discovered, it will delete itself from the infected phone. It can also be extricated via a command from the server.
What’s possibly even more impressive/frightening is that Chrysaor can remove itself from a device if it becomes compromised -- it can basically self-destruct.
To address the situation, the Android security team says that they have now “contacted the potentially affected users, disabled the applications on affected devices, and implemented changes in Verify Apps to protect all users.”
The nature of this attack, and the circa 36 devices out of more than 1.4 billion it infected, means that the chances of you being affected by it were already incredibly slim. Regardless, the Android team says suggests users adhere to these five basic steps to help keep themselves safe when using Android devices:
- Install apps only from reputable sources: Install apps from a reputable source, such as Google Play. No Chrysaor apps were on Google Play.
- Enable a secure lock screen: Pick a PIN, pattern, or password that is easy for you to remember and hard for others to guess.
- Update your device: Keep your device up-to-date with the latest security patches.
- Verify Apps: Ensure Verify Apps is enabled.
- Locate your device: Practice finding your device with Android Device Manager because you are far more likely to lose your device than install a PHA.
What are your thoughts on Chrysaor and the potential of such Android spyware apps? Let me know in the comments.